The Mirai Botnet has found itself back in the headlines after a barrage of new attacks using updated modules against D-Link, Netgear, and Sonic Wall devices and routers. The new updates bring with its abilities to target flaws never seen before in Internet-of-Things (IoT) devices. Since late February, groups using Mirai have been targeting six known vulnerabilities and three previously unknown ones. These exploits include:
- VisualDoor – a SonicWall SSL-VPN remote command injection vulnerability that came to light earlier this January
- CVE-2020-25506 – a D-Link DNS-320 firewall remote code execution (RCE) vulnerability
- CVE-2021-27561 and CVE-2021-27562 – Two vulnerabilities in Yealink Device Management that allow an unauthenticated attacker to run arbitrary commands on the server with root privileges
- CVE-2021-22502 – an RCE flaw in Micro Focus Operation Bridge Reporter (OBR), affecting version 10.40
- CVE-2019-19356 – a Netis WF2419 wireless router RCE exploit, and
- CVE-2020-26919 – a Netgear ProSAFE Plus RCE vulnerability
The three previously undisclosed command injection vulnerabilities were deployed against unknown targets, one of which, according to the researchers, has been observed in conjunction with a separate botnet by the name of MooBot.
Mirais longevity in the cybercrime community owes to the fact that its source code was publicly released in 2016, leading to slew of variants and updates since then. Its’ shifting nature has made it difficult to keep tabs on.
For the known vulnerabilities Mirai targeted, all have been patched. The only devices it is known to be affecting at current are devices without the latest updates. The unknown vulnerabilities are believed to be tied to IoT devices, a target group that Mirai has always gone after in its lifetime.
“We cannot say with certainty what the targeted devices are for the unidentified exploits,” Zhibin Zhang, principal researcher for Unit 42 stated, “However, based off of the other known exploits in the samples, as well as the nature of exploits historically selected to be incorporated with Mirai, it is highly probable they target IoT devices.”
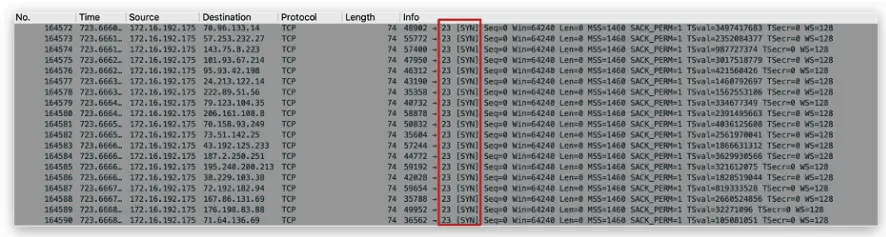
Mirai port scanning in February, observed by Unit 42
The exploits themselves include two RCE attacks — including an exploit targeting a command-injection vulnerability in certain components; an exploit targeting the Common Gateway Interface (CGI) login script (stemming from a key parameter not being properly sanitized). The third exploit targets the op_type parameter, which is not properly sanitized leading to a command injection, said researchers.
The latter has “been observed in the past being used by the Moobot botnet, however, the exact target is unknown,” researchers noted
Mirai: A Storied Botnet

The Mirai Botnet has been around for several years. While other malware may go into periods of slow activity, Mirai has remained at the forefront of botnet headlines since its inception.
Perhaps Mirai’s most infamous attack came on October 12, 2016. On that date, a massive denial of service (DDoS) attack left much of the internet inaccessible on the U.S. east coast. The attack, which authorities initially feared was the work of a hostile nation-state, was in fact the work of the Mirai botnet.
This attack, which initially had much less grand ambitions grew more powerful than its creators ever dreamed possible. The origins of the botnet were speculated for some time, many believing it to be the work of high-profile cybercriminals. Instead, Mirai was created by a group of three friends who were using the botnet to run an extortion ring on Minecraft servers, a video game they played together.
It encapsulated some clever techniques, including the list of hardcoded passwords. But, in the words of an FBI agent who investigated the attacks, “These kids are super smart, but they didn’t do anything high level—they just had a good idea.”
Much more damaging than simply developing the botnet, the creators released the source code publicly in 2016. This has lead to a wild fire of Mira-related attacks, and researchers estimate there are more than 60 variations of the botnet currently.
Mirai has a few key characteristics seen across all variations of it:
- Mirai can launch both HTTP flood and network-level attacks
- There are certain IP address ranges that Mirai is hard-wired to avoid, including those owned by GE, Hewlett-Packard, and the U.S. Department of Defense
- Upon infecting a device, Mirai looks for other malware on that device and wipes it out, in order to claim the gadget as its own
- Mirai’s code contains a few Russian-language strings. This was intended to be a red-herring on its origin, but still remains in variations
Protection
With evolving botnet tools like Mirai posing new threats every day, its important you use the tools required to protect your devices. One of these tools is SaferNet.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.