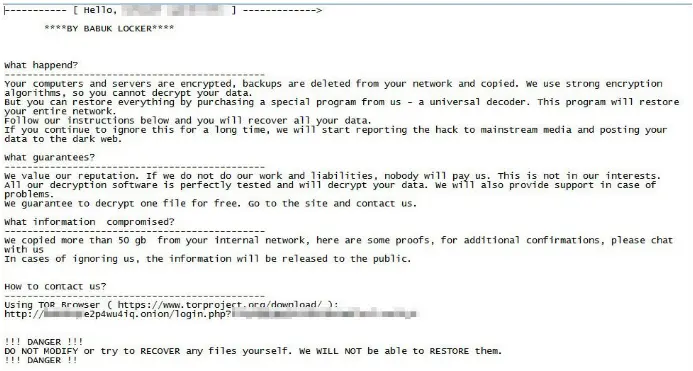
Identity Theft can be absolutely devastating for an individual. Usually, in the world of malware, we know certain things can be harmed. Our devices may need to be replaced, we may lose access to accounts for a few days or even forever, we may even need to pay a ransom for access to our data. The point is, with most types of Malware, we can eventually rebuild, though it may take longer than we anticipate. The fallout from identity theft is much longer.
Once your stolen information is used once, it can take anywhere from a few days to six months for that one incident. But your information is out there for a very, very long time. This means you could end up dealing with identity theft for many years, even decades.
Identity Theft has been around for a very long time and predates our modern technology by thousands of years. There have always been individuals that try to impersonate others for their own gain, financial or otherwise. However, the internet’s birth and wide adoption have led to new attack vectors, dwarfing any possible past attempts.
Now more than ever do we have data tied into our personal identity. Email addresses, banking numbers, phone numbers, social security numbers, home addresses – All of these and more form a picture of us as lines in a database.
And when this information falls into the wrong hands, it can do a lot of damage. Bank accounts can be drained, and your credit rating can get rattled; you can end up with medical bills or even a criminal record. The list of potential mishaps that can arise from identity theft is endless.
To hackers, identity theft represents a lucrative stream of income, and they can very easily cover their tracks. After they have seized personal information, they sell it on the dark web. This information can be sold over time, repeatedly, meaning that if you notice your identity has been stolen and used, it can be used in several instances over a long period of years.
There are some guidelines from the US government in discovering if you are a victim of identity theft if it is not immediately obvious:
- You stop receiving your regular bills and credit card statements.
- You receive statements for accounts you never opened.
- Debt collectors start calling you day and night about debts you’ve never heard of.
- The IRS alleges you failed to report income for a company you never worked for.
- You see withdrawals/charges on your bank or credit card statement that you didn’t make.
- You try to file your taxes only to discover that someone else beat you to it.
- You try to file your taxes and find someone claimed your child as a dependent already.
- Your credit report includes lines of credit you never opened.
- Your credit score fluctuates wildly and for no apparent reason.
- The most obvious sign—you receive a notification that you’ve been the victim of a data breach.
If you are unsure, it is always best to check with the authorities on the US government’s identity theft website.
There are two primary attack vectors when it comes identity theft online.
The first concerns a personal cyber attack that compromises your data. This takes place on your own devices, though usually, you are not aware of it. There is often a reliance on the user to fall for phishing scams or have inadequate cybersecurity protection. This will be covered in more detail later.
The other attack vector is through data breaches. These are exceptionally sophisticated large-scale attacks, usually on banks and hospitals. When a hacker breaches one of these institutes, they make off with thousands and often millions of records. These are immediately put up for sale on the Dark Web. Today, let’s look at 5 data breaches that caused identity theft on a large
Data Breaches That Caused Identity Theft #5: Yahoo!

The Yahoo! data breach doesn’t seem like an immediately obvious choice – Yahoo! do not operate as a bank or hospital, so do not store as much in-depth information about their users. However, the sheer scale of the breach meant that enough information was sold to commit identity theft.
To date, the Yahoo! breach is the largest and will likely remain so very a long time. While often referred to as one breach, the incident in-fact covers two breaches in 2013 but was not reported on until 2016. It was only in 2017 was the true scale of the damage was revealed.
In 2016, Wired and Vice’s journalists managed to secure an interview with an individual known online as Peace_of_Mind, or simply Peace. Peace revealed that he was working from a website on the Dark Web known as TheRealDeal. TheRealDeal had long been known to authorities; the site was a large part of the cyber arms industry and sold malware-as-a-service and personal data records for millions of people.
The website had been shut down by the time of the interview, and Peace was mostly retired. He informed the journalists that he acted as a broker; hackers would sell information to him, and he would sell to the masses. In the article, Peace names Yahoo! as one of the main sources of the information he sold.
It was only after the publication of the article that Yahoo! responded, stating they were aware of breaches. At first, they claimed 500 million users had their information stolen. In a second breach, they estimated it was about a billion accounts that had been compromised. Finally, in 2017, Yahoo! affirmed that 3 billion accounts had been compromised.
While Peace never revealed who sold him the information, the hackers were eventually caught. The four men accused include Alexsey Belan, a hacker on the FBI Ten Most Wanted Fugitives list, FSB agents Dmitry Dokuchaev and Igor Sushchin who the FBI accused of paying Belan and other hackers to conduct the hack, and Canadian hacker Karim Baratov who the FBI claimed was paid by Dokuchaev and Sushchin to use data obtained by the Yahoo! breaches to breach into about 80 non-Yahoo! accounts of specific targets.
The breach had a huge fallout, especially in the court cases against Yahoo!, many of which are still on-going. Because they did not tell their users there were breaches, Yahoo! has faced harsh criticisms. In 2018, a court settlement stated that anyone who could document that they were a victim of identity theft following the attack could receive money from Yahoo! from the settlement.
Data Breaches That Caused Identity Theft #4: JP Morgan Chase
In 2014, the JP Morgan Chase cyberattack and data breach was considered to be one of the most serious penetrations of America’s financial infrastructure to date.
4 hackers, 3 Israeli and 1 American began a series of spear-phishing attacks against JP Morgan Chase. Through these attacks, they intended to gain access to user accounts across Chases’ systems. In total, they got the details of 83 Million accounts, which covered 76 million households across the US.
Luckily, much of the data they stole was not fully revealing. It did not include social security numbers or passwords but did include names, addresses, emails, and phone numbers.
JP Morgan Chase and authorities acted immediately against the breach, and thankfully much of the information taken was unable to be sold online in time. The 4 involved in the scheme were quickly arrested and have since been sentenced.
While, thankfully, this data breach didn’t cause identity theft on a massive scale, it set a precedent. Banks could be breached – easily. The information could be taken, and if a hacker covered their tracks well enough, they had time to sell it.
Following the attack, JP Morgan Chase pledged a $150 Million cybersecurity budget per year and has given free credit monitoring to all involved in the breach to combat future instances of identity theft.
Data Breaches That Caused Identity Theft #3: Marriott Hotels

The Marriott Hotels breach was particularly harmful and long-lasting.
In 2016, Marriott purchased the Starwood Hotels and Resorts company. However, unknown to Marriott and Starwood was that since 2014 the Starwood databases had been breached by a Remote-Access-Trojan (RAT) and were actively being monitored.
During a routine security check-up in 2018, Marriott noticed unusual database queries within Starwoods database, from an individual with Administrator-level privileges. An investigation took place and it was discovered the person with those privileges did not make those queries – It was someone else controlling the account.
Database forensics revealed just how long the breach had lasted; at this point 4 years. It also revealed the scale – The information of 500 million guest records had been stolen.
For a hotel, this was a disaster. As well as names, emails, phone numbers, and addresses, credit card information and passport numbers were also stolen. Passport numbers in particular represent low-hanging fruit in the world of identity theft.
It is unknown who carried out the attack, but most signs point to Chinese military. Marriott have been involved in a number of class-action lawsuits, and the settlement has delivered a big pay-day for those affected by identity theft.
Data Breaches That Caused Identity Theft #2: Capital One

In July 2019, Capital One announced that they had undergone a massive data breach thanks to the actions of one hacker.
Months previous, a Seattle software engineer named Paige Thomas, had used the knowledge she gained while working for Amazon AWS Cloud Services to exploit an issue with Capital One’s internal firewalls and breach their systems. Thomas stole the records of 106 million people in the United States and Canada. This included social security numbers, which are the keys to commit identity fraud in the US.
Immediately after the attack, Thomas sold the data across sections of the Dark Web. Much of this data has yet to been used, so those affected may not even be aware somebody else has their information.
Thomas’s downfall was her hubris; After selling the data, she bragged about the attack in several hacking forums online. A common misconception about the hacking community is that they’re mostly criminals. Instead, the opposite is true, and her identity was revealed by several white-hat hackers within the community. She was swiftly arrested.
Capital One has been criticized for their response to the attack, specifically as they denied social security numbers and account numbers had been compromised, which later proved to be untrue. They are currently involved in many lawsuits as well Amazon and Github, who are accused of having knowledge of the exploit but not acting upon fixing it.
Data Breaches That Caused Identity Theft #1: Equifax
The Equifax breach is probably the best-known of all data breaches to have occurred. The personal, financial, and political fallout from the Equifax breach has been staggering.
Equifax is a credit reporting bureau and assesses the financial health of nearly every individual across the US. In March 2017, poor security practices led the data of 150 Million Americans being stolen, along with the personal information of 15 Million British citizens.
Several failures on Equifax’ part made the attack possible. Hackers exploited a vulnerability on the web portal at first; this vulnerability had been known for months yet the company hadn’t patched it out. Following this, the hackers were able to freely move around Equifax servers. This, again, is a cybersecurity flaw – Equifax failed to segment their servers correctly, leading to this kind of movement. Finally, Equifax had failed to renew encryption certificates for months – Which meant the hackers could pull out information undetected.
When Equifax realized the breach, they did not report on it for several weeks. Sales of Equifax stock at the time before the announcement have led to speculation that insider trading took place here.
The data stolen included nearly everything you could know about someone – name, address, email, phone number, social security number, credit card number, even their driver’s license number.
The identity theft fallout from Equifax is not what you’d expect. Following the incident, many in the information security community monitored the Dark Web for bulks of data appearing in stores. This never really happened – There was a trickle of data, but never any large drop. Millions had their data sold, but not the 150 million as expected.
This pointed to a possible culprit – state-sponsored hackers. Sure enough, in a rare move, the Department of Justice charged 4 members of the Chinese military in early 2020. This is considered rare because foreign military intelligence operatives are not often charged with criminal charges.
This has brought about a theory that the Chinese military was not all too interested in selling the data but perhaps were using it for espionage. It is unknown what the Chinese military would do with 150 million social security numbers, but perhaps the story is not fully told yet.
What you can do to Prevent Identity Theft
In the above cases, the individuals who had their information leaked were not at fault, rather it was corporations that were held responsible.
These are cases of large-scale data breaches, but every-day identity theft occurs most often on a personal scale.
Phishing attacks, Spyware, and Botnets are all used against us daily to uncover our details, and most of us do not have adequate protection.
SaferNet was engineered with threats like identity-theft in mind.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.