Anew malware has surfaced in the wild, dubbed Saint Bot. The Saint Bot Malware is deployed via phishing emails and aims to deploy credential stealers and download other malware strains onto target devices. Saint Bot was first spotted in January 2021; however, a surge of reports of infections along with the strain showing new features points to the idea that Saint Bot is under active development and may very well prove to be a major threat in the coming months.
According to cybersecurity researchers at MalwareBytes, Saint Bot has been gaining slow momentum in the cybercrime world. Researchers noted the malware dropping stealers such as Taurus Stealer and other loaders. It has been designed so that it is a suitable launching point for just about any malware strain.
“Saint Bot employs a wide variety of techniques which, although not novel, indicate some level of sophistication considering its relatively new appearance.” researchers said.
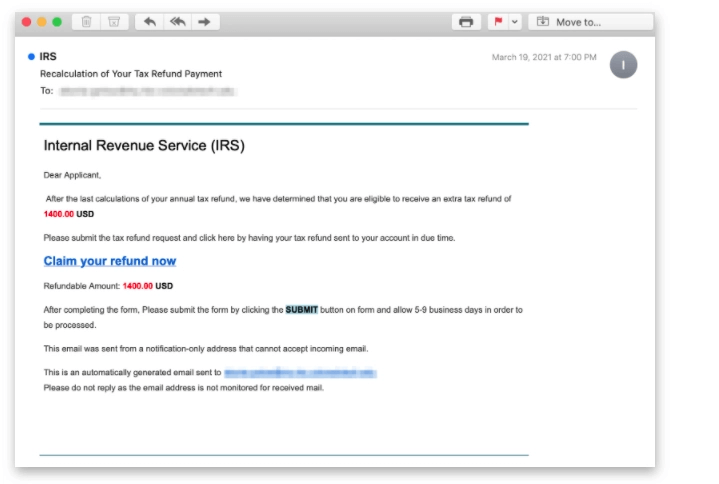
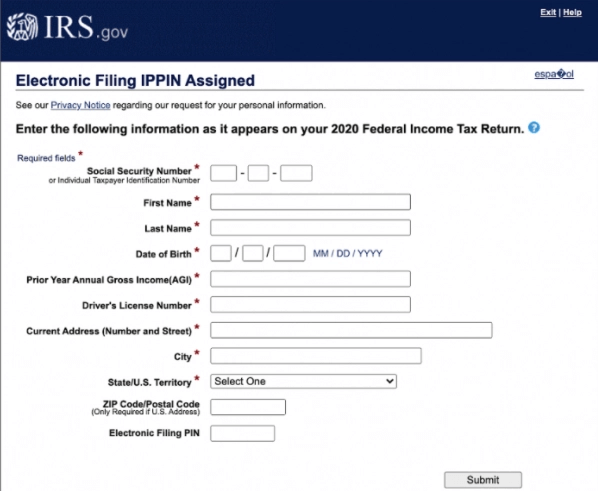
The infection chain analyzed by the MalwareBytes begins with a phishing email containing an embedded ZIP file (“bitcoin.zip”) that claims to be a bitcoin wallet when, in fact, it’s a PowerShell script under the guise of .LNK shortcut file. This PowerShell script then downloads the next stage malware, a WindowsUpdate.exe executable, which, in turn, drops a second executable (InstallUtil.exe) that takes care of downloading two more executables named def.exe and putty.exe.
The payloads for Saint Bot, interestingly, are hosted on Discord. This tactic is becoming popular for hackers, who abuse the functionality of legitimate services for Command-&-Control (C&C) communications, security evasion, and to deploy Malware.
“When files are uploaded and stored within the Discord CDN, they can be accessed using the hardcoded CDN URL by any system, regardless of whether Discord has been installed, simply by browsing to the CDN URL where the content is hosted,” researchers from Cisco Talos disclosed in an analysis earlier this week, thus turning software like Discord and Slack into lucrative targets for hosting malicious content.
“Saint Bot is yet another tiny downloader,” researchers said. “It is not as mature as SmokeLoader, but it is quite new and currently actively developed. The author seems to have some knowledge of malware design, which is visible by the wide range of techniques used. Yet, all the deployed techniques are well-known and pretty standard, [and] not showing much creativity so far.”
Saint Bot Malware Analysis

The bulk of this analysis was carried out by researchers at MalwareBytes, notably by Aleksandra “Hasherezade” Doniec.
As mentioned previously in this article, the first step of the attack is via a phishing email purporting to be a bitcoin wallet. The wallet is a decoy, and instead was in fact an obfuscated PowerShell script that would infect the host with Saint Bot. While the majority of cases have used the bitcoin wallet set-up, Hasherezade noted that the same attack targeted government institutions in Georgia recently, acting as a COVID-themed campaign.

One the script is run, the main sample drops another executable in the %TEMP% directory. This then downloads two executables named: def.exe, and putty.exe. It saves them in %TEMP% , and tries to execute them with elevated privileges. If run, the first sample (def.exe) deploys a batch script disabling Windows Defender. The second sample (named putty.exe) is the main malicious component.
The scripts from the “AppData/Local/z_[user]” are used to deploy the main sample. During the first run, the executable injects itself into “EhStorAurhn.exe“. Below we can see the injected implant detected and dropped by HollowsHunter.

Once the implant was injected, it connects to its Command-and-Control server (C&C) and proceeds with its main actions. Observing the network traffic we will find the URL of the malware’s C&C queried repeatedly:
http[:]//update-0019992[.]ru/testcp1/gate.php
Following this URL we can see the related C&C panel, which looks typical for the Saint Bot:

From here, the hackers are able to trigger commands from the C&C, including downloader further malware strains.
Researchers noted the evolution of the code between the current sample and a sample from January. While January’s contains the same C&C, the code is rewritten. It used a mutex “saint2021_NewGeneration” suggesting that this bot went through some major changes since the beginning of this year.
Protection
The Saint Bot Malware is just another example of new malware strains infecting machines globally. Furthermore, it highlights the issue with phishing – The phishing attack vector is still key to a hackers success, and the weakest link in business cybersecurity.
It is important that business leaders use proactive phishing protection tools to sure their businesses aren’t affected by malware attacks. One of these tools is SaferNet.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.