Malware often makes its nest in crisis areas. Individuals looking for aid, financial or otherwise, are key targets for phishing lures put out by hackers. These crisis-focused campaigns can be lucrative but are often looked down upon even in the most radical black-hat hacking circles. Regardless of the ethics behind the behavior, the American Rescue Act has proved to be an opportunity too tempting to pass up for a group of hackers targeting individuals seeking financial aid via stimulus checks.
The act itself was recently signed into law and aims to give financial aid to Americans, especially those hit particularly hard by the economic downturn caused by the pandemic. The act sends Americans who earn under a certain threshold a stimulus amount of $1,400 each.
Hackers see a payday for themselves here, and since early March, one group has been involved in an email phishing campaign, purporting to be the IRS. The group uses the IRS logo and even spoofs the sender domain in a reasonably convincing manner. The email says, “It is possible to get aid from the federal government of your choice” and then offers “quotes” for too-good-to-be-true things – such as a $4,000 check, the ability to “skip the queue for vaccination” and free food.
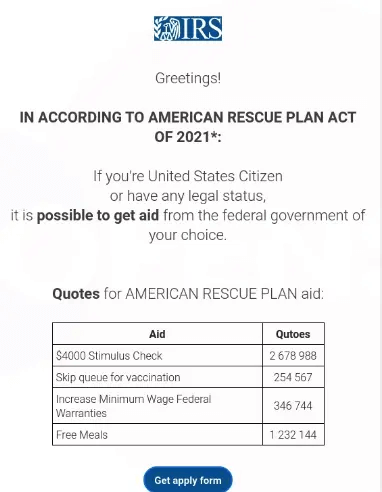
Phishing Email Used In The Campaign
If the target clicks “Get apply form,” they’ll be taken to an Excel sheet which states, “Fill this form below to accept Federal State Aid.”. The catch here is that the user is told that they must enable content macros if they wish to see the document in its entirety. Doing this will enable macros that set off a chain that will deploy the Dridex banking trojan on their machine. Dridex is a veteran in the banking malware scene and will siphon any and all banking credentials off an infected machine without a user’s knowledge.
Phishing attack prevention researchers Confense have been investigating the campaign. “While static analysis easily identifies the URLs used to download malware in this case, automated behavioral analysis may have trouble recognizing the activity as malicious because it does not use macros to directly download malware or run a PowerShell script,” researchers explained, in a posting on Tuesday. “The macros used by the .XLSM files drop an .XSL file to disk, and then use a Windows Management Instrumentation (WMI) query to gather system information.”
WMI is a subsystem of PowerShell that gives admins access to system monitoring tools, including the ability to ask for information about anything that exists on a given computer – such as which files and applications are present. It can also request responses to these queries to be given in a certain format.
“The WMI query employed in this case…demands that the dropped .XSL file be used to format the response to the query,” researchers wrote. “This formatting directive allows JavaScript contained in the .XSL file to be executed via WMI and download malware, avoiding the more commonly seen methods via PowerShell.”
Dridex Malware Origins
Dridex is an older strain of malware, first being reported a decade ago in 2011. It also goes by the names Bugat and Cridex. Dridex is mostly commonly deployed via phishing emails, and it generally targets banking credentials.
Dridex’ gain in popularity was comparatively slow, but by 2015 it had become the worlds foremost financial trojan. Most often, Dridex campaign targeted corporate emails. This lead to later versions of the Malware being updated to include ransomware deploying capabilities. Furthermore, Dridex developed increased obfuscation techniques as corporate anti-virus grew more sophisticated.
The original developers of Dridex are believed to be a Russian cybercrime group named ‘Evil Corp.’ (No points for originality!). In December 2019, authorities cracked down on the group with sanctions and charges against its leader, Maksim Yakubets, known for his lavish lifestyle. U.S. authorities are still offering up to $5 million for information leading to his arrest; they allege that Yakubets and Evil Corp. have stolen millions of dollars from victims using the Dridex banking trojan and Zeus malware.
Prevention
As with all phishing campaigns, they key to prevention is education. When reading emails, look for errors and keep a suspicious eye. Be wary of “too good to be true” claims, and keep up to date on government plans on distributing aid like seen with the American Rescue Act.
Beyond education, there are tools that can protect your home and business against Malware attacks like Dridex. One of these tools is SaferNet.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.