Malware developers use a variety of methods to avoid detection. An on-going campaign highlights one of these methods – Coding in an obscure programming language to bypass security defenses. Since February 3rd, threat actor TA800 has carried out a spear-phishing campaign to deliver their new Malware loader, NimzaLoader. NimzaLoader is programmed in Nim, an imperative, general-purpose language with syntax similar to Python. Nim is an uncommon language, meaning reverse-engineering NimzaLoader can be tricky, and security tools may be unable to analyze it.
TA800 has a long cybercrime history, and NimzaLoader seems to be a less-detectable version of a previous loader of theirs, BazaLoader. The campaign thus far has used highly-targeted spear-phishing and has claim 100 victim organizations across 40 industries.
The full extent of NimzaLoaders’ capabilities is not yet fully clear, but it has been reported as distributing Cobalt Strike. Cobalt Strike is a sophisticated Malware that has a host of tools at its hands, including keylogging, file transfer, SOCKS proxying, privilege escalation, mimikatz, port scanning, and lateral movement. It is sold as Malware-as-a-Service (MaaS).
Consistent with previous campaigns, TA800 uses personalized details in the email lure, including the recipients’ name and company name.
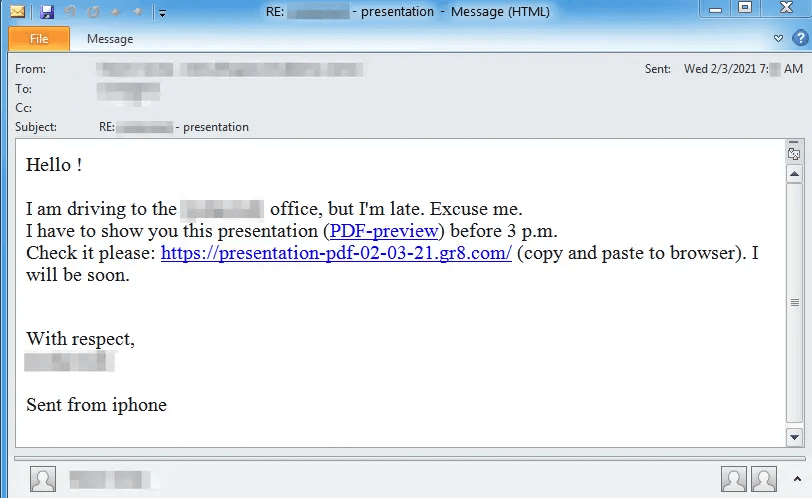
The message contains a link, often shortened or obscured, purporting to be a link to important business PDF documents. Following the link, the target will be brought to a landing page with a link to the PDF. The link is disguised with Adobe logos and is hosted on Slack.
Downloading the file will immediately deploy NimzaLoader to the users’ machine, though it is unlikely they will experience any immediate changes. Use of the Nim programming language means the Malware can slide past file-scanning programs effortlessly. Once on the machine, NimzaLoader will drop Cobalt Strike, and the damage will begin.
NimzaLoader Malware Analysis

Much of this analysis has been carried out by cybersecurity researchers at Proofpoint.
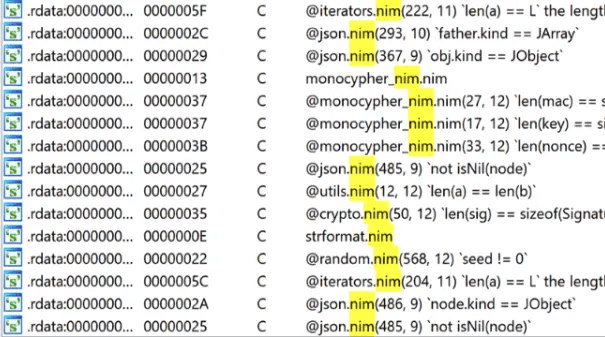
NimzaLoader was developed using the Nim programming language, which can be seen various ‘Nim’ related strings in the executable:
TA800 has been active in the cybercrime scene for a few years and is mostly known as affiliate distributors. Affiliate distributors rarely write their own Malware and use MaaS in their attacks.
TA800 has mostly been active in North America and has targeted a wide range of industries. Usually, they are known for distributing banking trojans and malware loaders. The group is also known for carrying out several spear-phishing attacks. The attacks always include some sense of urgency for the users to carry out instructions. Some of these lures have included hard-to-resist subjects such as payment, meetings, termination, bonuses, and complaints in the email’s subject line or body.
The hackers made headlines in late 2020 when they carried out a series of attacks on the healthcare sector using a malware loader named BazaLoader. When hospital systems became infected with Bazaloader, it dropped Ryuk as a payload. Ryuk is a notorious Ransomware we have covered in previous articles.
Protection
In many forms of cyberattacks, but especially those of a phishing nature, education and intuition are key to protection. Being able to discern a legitimate email and a phishing email is a skill that is the first line of defense. In small businesses, employees should receive regular cybersecurity training to learn the signs.
Beyond training, there are tools out there that can prevent attacks like phishing. One of these tools is SaferNet.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.