Phishing, in one way or another, has been around longer than the internet or computers have. Phishing is an act in which an individual presents a fraudulent persona to gain trust and obtain something that doesn’t belong to them.
This fraudulent persona could really be a persona, or it could be a website, or an invoice, or an official document.
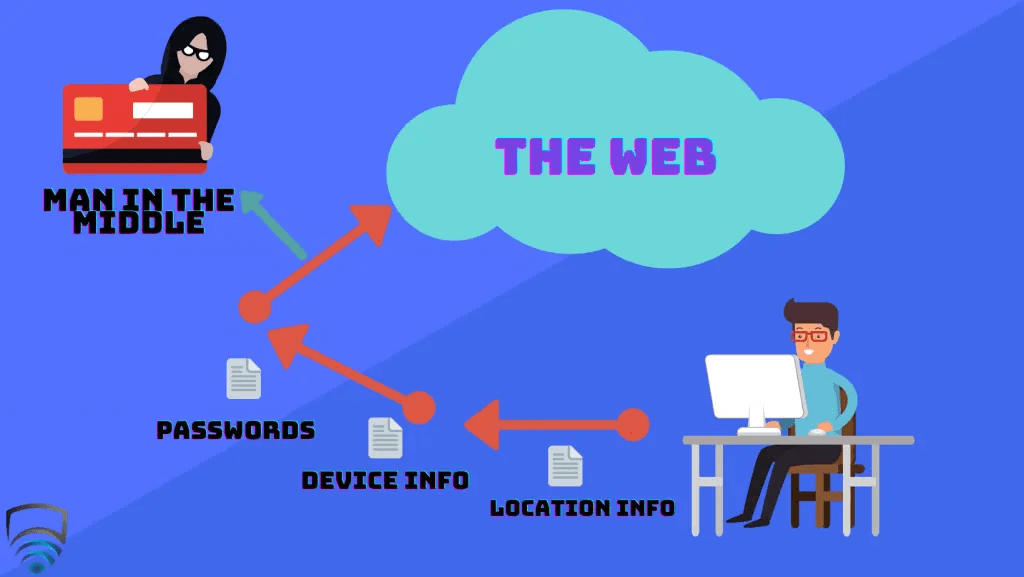
What they seek to gain could be money, passwords, login credentials, email lists, or other sensitive and private information.
There are many different attack methods in Phishing scams. It occurs over mail, phone calls, texts, but most frequently over email.
In our own lives, we are most used to seeing bulk phishing. This involves sending out mass texts or emails to large groups of individuals. Usually, these will include a link to a website that appears like an email login page we’re used to seeing, or Google, or really just about any service. It will ask us our login credentials and many people will willingly give them over, unaware that the page they’re on is a decoy for hackers to harvest information. Another common method here is to pose as a postal service requesting a fee for taxes or shipping. The fee may be small but this is done so successfully and so regularly it adds up quickly.
When Phishing makes the news, it’s usually Spear Phishing and specifically Whaling. Rather than sending out bulk messages, Spear Phishing is more precise and will go after a smaller group of individuals and employ a high degree of social engineering to extract the required information. Whaling is the natural conclusion to Spear Phishing – Whaling involves targeting high-level executives, managers, or other individuals of positions of power.
Seeing those headlines, you might think the attacks only go after the billion-dollar corporations or governments but that would be incorrect; Most of these attacks are carried out on small, medium, and large businesses. These kinds of attacks are known as Business Email Compromise (BEC), and every business no matter the size should educate employees on the dangers of BEC. The FBI has put the total cost of BEC between 2016 and 2019 at $26 billion in the United States.
Though the corporate world is certainly the biggest target for the hackers behind Phishing attacks, all of us are at risk in our private lives. Read on to learn more about the most harmful types of Phishing emails that you, your business, or your family can face.
The Invoice Scam
The invoice scam, or invoice fraud, is one of the earliest forms of phishing which predates the Internet.
This occurs when your business or private email receives an Invoice that is not legitimate. The degree of success for the hacker here balances on a few factors. At home, you are aware of all the household work being carried out, and if any large invoices were coming in you’d expect them, and so could see through this. The smaller invoices may go unnoticed though, like the taxes and shipping fees we mentioned earlier.
For a business, this can get a little tricky. Oftentimes a business as multiple invoices at once, and it can be difficult to tell the real and fake apart. In 2019, Scott County Schools in Kentucky announced it had been hit by a major invoice scam, where they paid out $3.7 Million to an invoice that was “overdue”.
It isn’t just schools falling for this either – In 2019 again, and individual named Evaldas Rimasauskas scammed Facebook and Google with invoices, and made off with $100 million before being discovered.
The Executive Imposter Scam

Executive Impersonation is an exceptionally successful form of Phishing. There is a thought that it is so successful because many businesses think they are too small to be targeted, but this is incorrect. Simply having a company LinkedIn with a visible hierarchy makes you a target.
In this type of Phishing, a hacker will pretend to be a high-level executive within the company, usually the CEO, President, etc. They will identify who in the company is responsible for handling money and send out emails to transfer money to another account – Which, of course, belongs to the hacker.
It may seem unlikely that a business could fall for this, but the hacker will often know the companies inner workings. This could be gained through social engineering techniques or using other forms of Malware, especially Spyware.
If somebody in your business contacts you and you’re unsure of their true identity – Call them.
Email Contacts Spam
Email Contacts Spam is a form of phishing that not only takes elements of bulk phishing but nearly always uses some form of other Malware in taking its initial steps.
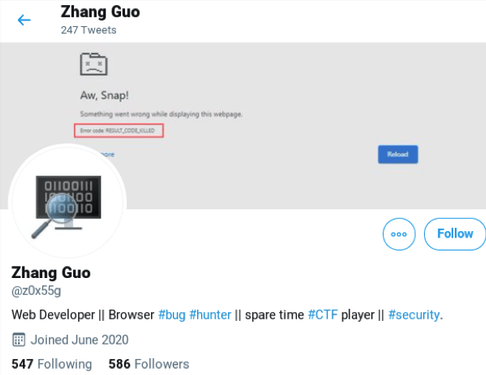
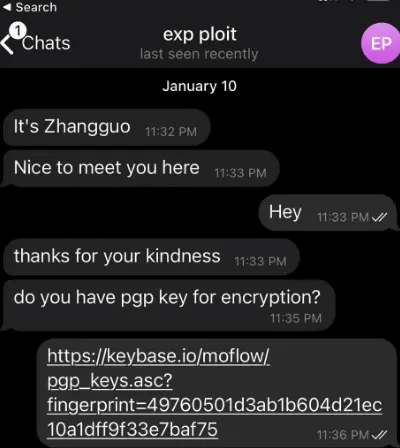
A hacker will target usually one person in the company, whose email they have obtained through another phishing attack, or using Spyware. For it to work, the target must remain unaware they have been compromised.
When the hacker has access to the victims’ email account, they will study company emails to learn the language used, the types of emails sent, and what positions everyone has within the company.
They will then take to the victims’ contact list, sending out a mass of emails to all relevant targets within the company requesting money transfers.
This attack is tricky to pull off successfully, but if pulled off successfully can be lucrative for the hacker and devastating for the business.
Attorney Impersonation
The Attorney Impersonation scam is a type of Phishing that can affect business and residential targets equally.
Like the Executive scam, high-end Attorney Impersonation will often involve a large degree of social engineering, and study of the target’s habits and personal information.
These hackers most commonly impersonate the Department of Justice and will pose as an investigator. They will request personal information from the target, who will often hand it over. This particular type of Attorney Impersonation targets the elderly and senior citizens most commonly.
Companies who regularly deal with attorneys must be cautious here also. Hackers will pose as attorneys, looking to settle fees or impose other invoices. If an attorney you know is being impersonated, you should always try to call the real individual if you suspect something is amiss.
Data Theft
Data Theft Phishing emails are the most common and most destructive of the methods talked about in this article.
Employees, or family members, will receive an email, which will lead to a fake login screen. The login screen can mimic just about anything; Email accounts, social media, banking, and IRS. Compromising one or more of these accounts can be devastating. Not only is the individual compromised, but it can be used as a launchpad to begin many of the other attack vectors listed above.
Data Theft emails like these can have a domino effect. If someone with a lower rank in the company is breached, the hacker can use their account to get access to someone higher up in the company, and so on until they get C-level access.
With that in mind, security and vigilance against this shouldn’t be reserved just for those at the top but needs to be company-wide to be successful.
Protection against Phishing
No form of protection against Phishing is 100% effective, and beyond doubt, your most useful tool is education. Social engineering is the lifeblood of Phishing, and most forms will fall flat if it doesn’t work. Educating yourself, employees, and family members on spotting what’s fake will secure you as nothing else will.
Even with education, Phishing can still be successful. In years gone, fake login pages were obvious and any familiarity with the real thing would make it immediately clear. In more modern times, these have instead become high-fidelity copies, and any social engineering that goes along with them can nearly be flawless.
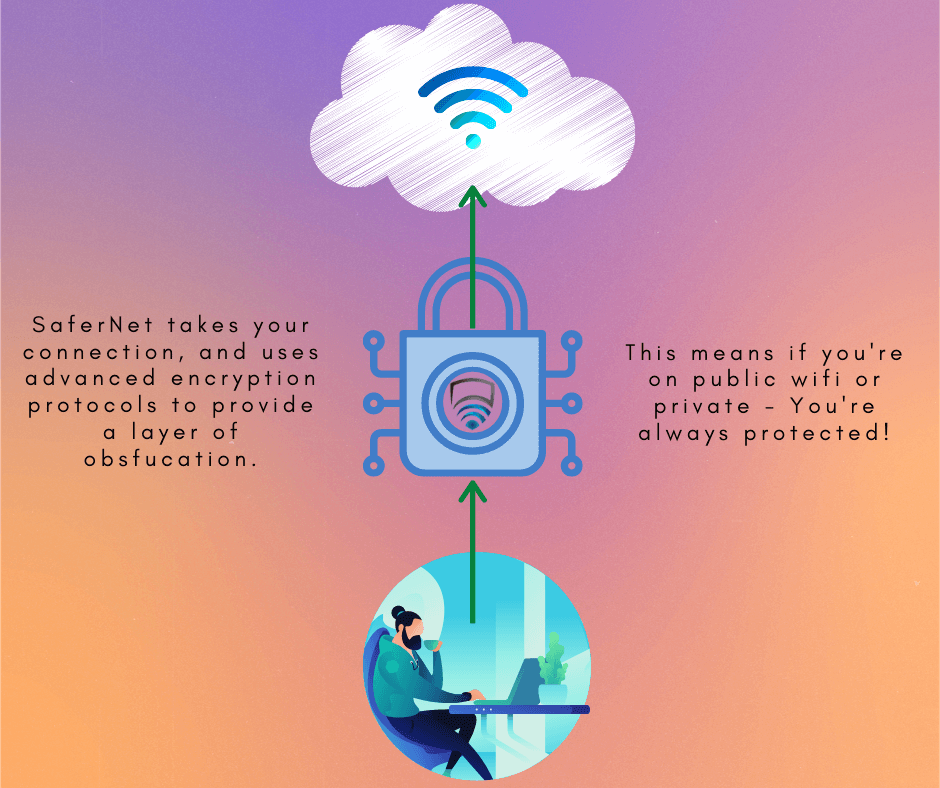
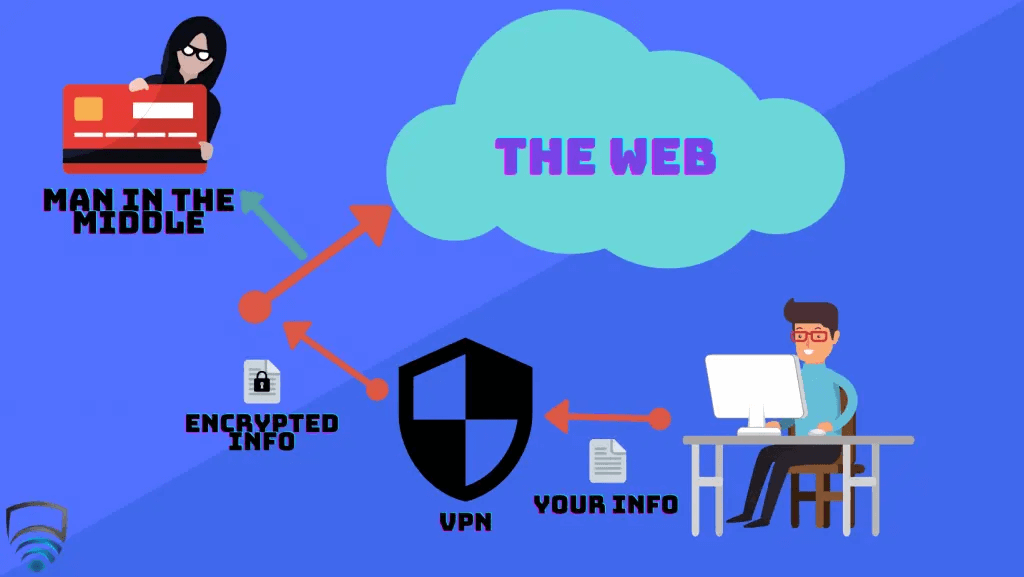
For times like these, SaferNet can help fill in the gaps of education when the difference is too small to tell apart.
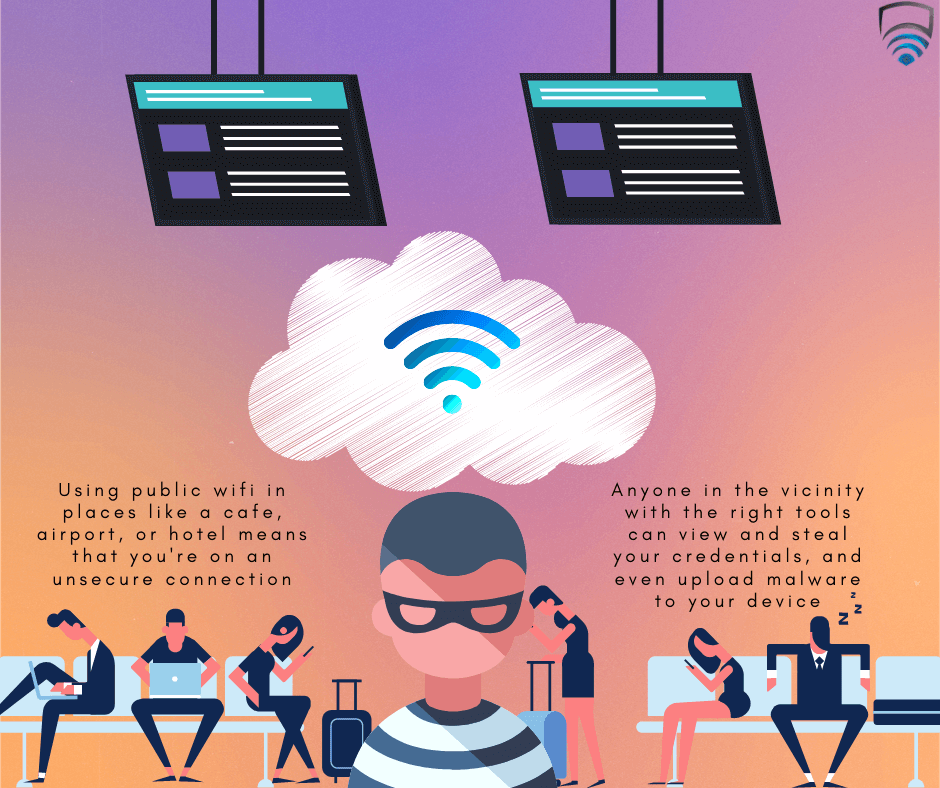
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.