Braktooth is the name given to a new set of security vulnerabilities that affect Bluetooth devices and can enable a hacker to execute arbitrary code or crash devices via denial-of-service (DoS) attacks.
Braktooth (referring to the Norwegian word “Brak” which translates to “crash”) contains 16 weaknesses which span across 13 Bluetooth chipsets from 11 vendors such as Intel, Qualcomm, Zhuhai Jieli Technology, and Texas Instruments, covering an estimated 1,400 or more commercial products, including laptops, smartphones, programmable logic controllers, and IoT devices.
Braktooth was discovered by cybersecurity researchers from SSET (Automated Systems SEcuriTy) at the Singapore University of Technology and Design (SUTD).

“All the vulnerabilities […] can be triggered without any previous pairing or authentication,” the researchers noted. “The impact of our discovered vulnerabilities is categorized into (I) crashes and (II) deadlocks. Crashes generally trigger a fatal assertion, segmentation faults due to a buffer or heap overflow within the SoC firmware. Deadlocks, in contrast, lead the target device to a condition in which no further BT communication is possible.”
Of the 16 vulnerabilities, the most severe is CVE-2021-28139, which affects the ESP32 SoC used in many Bluetooth-based appliances ranging from consumer electronics to industrial equipment. Due to a lack of an out-of-bounds check in the library, an attacker can inject malicious code on vulnerable devices.
Other Braktooth vulnerabilities can result in Bluetooth functionality getting entirely disabled, or cause a DOS condition in laptops and smartphones employing Intel AX200 SoCs. “This vulnerability allows an attacker to forcibly disconnect slave BT devices currently connected to AX200 under Windows or Linux Laptops,” the researchers said. “Similarly, Android phones such as Pocophone F1 and Oppo Reno 5G experience BT disruptions.”
Bluetooth speakers, headphones, and audio modules can be sent into a bricked-state byBraktooth, where the user will be unable to turn them back on. The Braktooth attacks can be carried out using a readily available Bluetooth packet sniffer that costs less than $15.
A handful of companies including Espressif and Infineon have released firmware patches to protect vulnerable devices, while Intel, Qualcomm, and others are still investigating and a patch is in the works. Texas Instruments doesn’t intend to release a fix unless “demanded by customers.”
Braktooth Vulnerability Analysis
Note: This analysis was carried out by ASSET.
The attacker only requires (1) a cheap ESP32 development kit (ESP-WROVER-KIT [31]) with a custom (non-compliant) LMP firmware and (2) a PC to run the PoC tool. The PoC tool communicates with the ESP32 board via serial port (/dev/ttyUSB1) and launches the attacks according to the specified target BDAddress () and exploit name parameter ().
Below are the devices used for evaluation of Braktooth. The sample code is provided by vendor to test the development board. This is not applicable (N.A) on products running a fixed application.

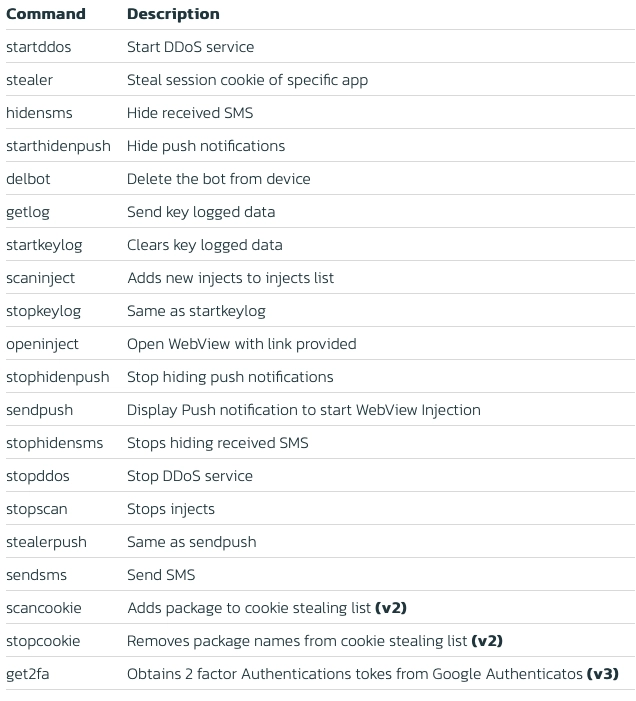
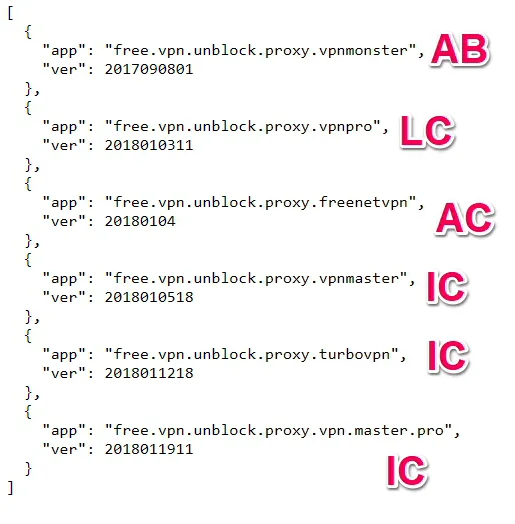
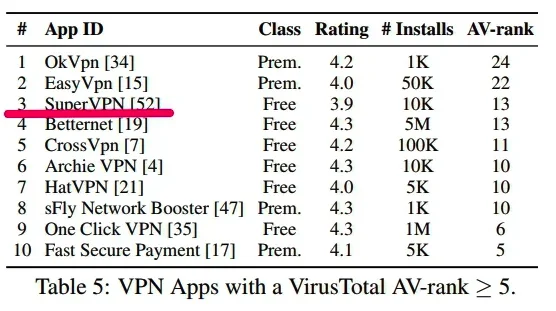
Below is a summary of new vulnerabilities and other anomalies found (Vx: Vulnerability, Ax: Non-compliance) which make upBraktooth.

A summary of Braktooth appears in Table 2. In each row, we use the prefix V to identify a security vulnerability and A to indicate an anomalous behaviour (i.e., faulty target responses) that deviates from the Core Specifications [27]. Moreover, Table 2 outlines the respective CVEs, affected devices, protocol layers, and the violated compliance. In summary, we discovered 16 new security vulnerabilities belonging toBraktooth. For all the discovered vulnerabilities, we have followed a responsible disclosure process.
The impact of our discovered vulnerabilities is categorized into (I) crashes and (II) deadlocks. Crashes generally trigger a fatal assertion, segmentation faults due to a buffer or heap overflow within the SoC firmware. Deadlocks, in contrast, lead the target device to a condition in which no further BT communication is possible.
This may happen due to the paging scan being forcibly disabled (V16), state machine corruption on V6 or entirely disabling BT functionality via arbitrary code execution (ACE) on V1. Our results affect popular BT vendors (i.e, Intel, Qualcomm, Cypress, Texas Instruments) and relatively less known (i.e., Bluetrum, Jieli Technology, Harman), which are still employed in many consumers products such as BT speakers, keyboards, toys, etc.
V1 affects ESP32, which is used in many products ranging from consumer electronics to industrial equipment such as programmable logic controllers (PLCs). Hence, the impact is significant, as the attacker only requires knowledge of the target BDAddress to launch the attack. Indeed, all the vulnerabilities V1-V16 can be triggered without any previous pairing or authentication. Moreover, the impact of V1-V16 reaches beyond the devices listed in Table 2, since any other BT product employing an affected SoC is also vulnerable.
Multiple Link Manager Protocol (LMP) flooding attacks (e.g., V4, V12) and V15 were detected across SoCs from different BT vendors. Since the affected vendors are majors in their fields (i.e., Intel & Qualcomm), it indicates that there is a lack of flexible tools for over-the-air testing even in 2021. Besides, the Core Specifications only allows a limited “LMP test mode” [27] that restricts the SoC to operate with few LMP procedures.
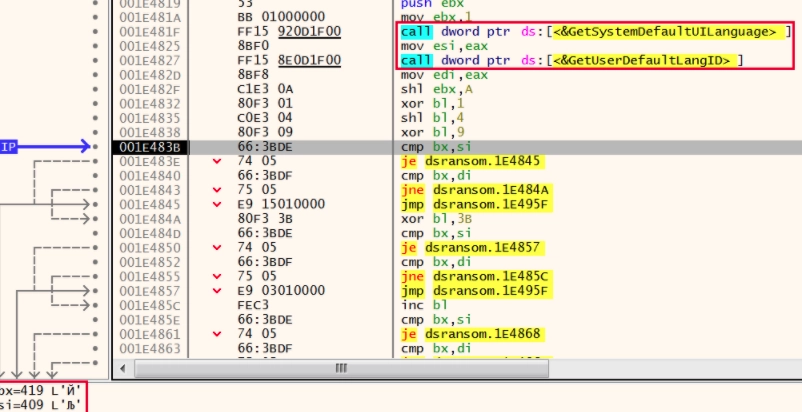
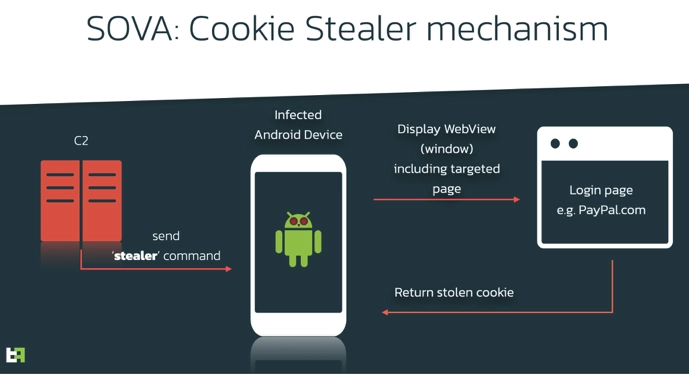
The most critical vulnerability ofBraktooth (V1 in Table 2 – 8.1) affects ESP32 SoC [30], which is used in many Wi-Fi and Bluetooth IoT appliances such as Industry Automation, Smart Home, Fitness, etc. The attack is illustrated in Figure 3. A lack of out-of-bounds check in ESP32 BT Library [9] allows the reception of a mutated LMP_feature_response_ext. This results in the injection of eight bytes of arbitrary data outside the bounds of Extended Feature Page Table (“E. Features Table” in Figure 3).
An attacker, which knows the firmware layout of a target device, can write a known function address (JMP Addr.) to the offset pointed by Features Page (“Feat. Page” in the LMP_feature_response_ext packet) field. It turns out that the BT Library stores some callback pointers within the out-of-bounds Features Page offset and such a callback is eventually invoked during the BT connection.
While exploiting this vulnerability, we forced ESP32 into erasing its NVRAM data (normally written during product manufacturing) by setting JMP Addr. to the address of nvs_flash_erase. Such erase function is always included in ESP32 SDK [7] and therefore, it is present in any ESP32 firmware. Similarly, disabling BT or BLE can be done via esp_bt_controller_disable and Wi-Fi via disable_wifi_agc.
Additionally, general-purpose input/output (GPIO) can be controlled if the attacker knows addresses to functions controlling actuators attached to ESP32. As expected, this has serious implications if such aBraktooth attack is applied to Bluetooth-enabled Smart Home products.

Protection

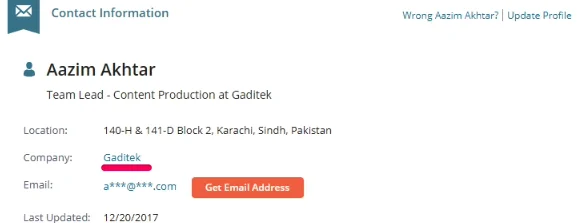
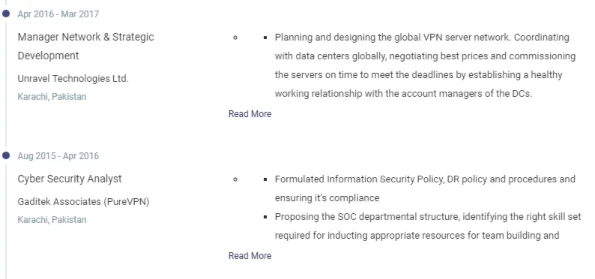
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.