BlackMatter Ransomware struck over the weekend, targeting business software solutions provider Marketron. Marketron is a growing business and has more than 6,000 customers in the media industry. It provides cloud-based revenue and traffic management tools for broadcast and media organizations. The company specializes in revenue management and audience engagement, handling advertising revenue of $5 billion every year.
Marketron customers were informed of the BlackMatter Ransomware attack in an email on Sunday night from the company CEO, Jim Howard, who said that “the Russian criminal organization BlackMatter” was responsible for the attack.
The BlackMatter Ransomware gang is seemingly ramping up operations – Last week SaferNet reported on a BlackMatter breach within the NEW Cooperative U.S. farmers organization, which demanded a $5.9 million ransom.
Howard is apologetic in the email to his customers, stating that they are unaware of how the BlackMatter Ransomware gang breached the network, given that Marketron has made significant investments recently in cybersecurity implementations designed to protect from intruders.
“This issue comes despite significant recent investments in separating backup and disaster recovery in different physical and network environments, instituting ‘zero trust’ access management policies, and new security detection and recovery tools”, Howard said in the email.
He went on to state that the company is in contact with both the BlackMatter Ransomware gang and the FBI, and that all efforts are being made to restore systems as soon as possible.

Marketron publically announced the incident this morning, stating that it was dealing with a “cyber event” that disrupted some of its business operations and impacted all its customers.
“Currently, all Marketron services are offline,” the company announced, adding that the attack affected the Marketron Traffic, Visual Traffic Cloud, Exchange, and Advertiser Portal services.
RadioTraffic and RepPak services were still standing but the company took them offline as a precaution. The only platforms that remained online were Pitch, Email Marketing, and Mobile Messaging.
Bo Bandy, VP of Marketing at Marketron, said in the disclosure that third-party forensic investigators were working “to understand the full nature and scope of the event, determine root cause, and to ensure the integrity, safety, and security of our systems and data.”
“We are unable to confirm the root cause of the event at this time and this investigation is very much on-going” Bandy said.
BlackMatter Ransomware is believed to be a rebrand of Darkside Ransomware, which took Colonial Pipeline offline in May.
The gang have been extremely active this month alone and has a gallery of victims including:
- a wine and spirits company
- an investment banking services provider in the U.S.
- a vendor of citrus juicing equipment in Austria
- a maker of drilling and foundation equipment in Italy
- Japanese technology giant Olympus
- a US-based construction company
- a unified communications company in the UK
BlackMatter Ransomware Analysis
Note: This analysis was carried out by Sophos Labs
The Sophos research is based on a sample of the BlackMatter ransomware, with the SHA-256 hash: 22D7D67C3AF10B1A37F277EBABE2D1EB4FD25AFBD6437D4377400E148BCC08D6.
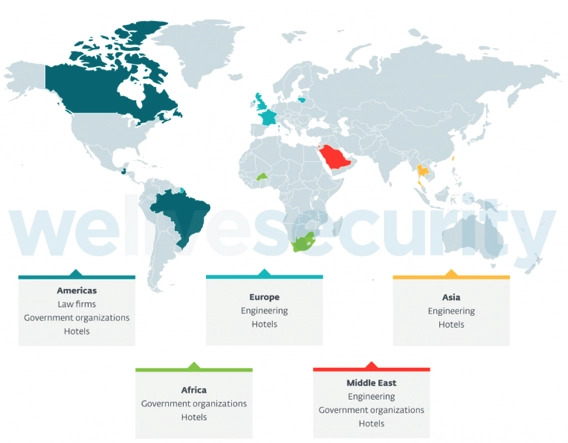
The operators behind the BlackMatter RaaS have established a presence on the dark web:

The list of sectors and entities this threat actor says it will not attack reflect the recent global incidents involving DarkSide (Colonial Pipeline) and REvil (Kaseya) ransomware, which drew widespread and probably unwelcome attention.
The operators behind BlackMatter claim that their ransomware incorporates the best features of DarkSide, REvil, and LockBit 2.0 ransomware. They also say that while they are closely acquainted with the Darkside operators, they are not the same people – this idea has been contested by researchers.
Below is a short comparison of some of the capabilities seen in the various groups:

When victims are hit with the BlackMatter ransomware and the files on the drives are encrypted, BlackMatter sets a wallpaper that is very similar to DarkSide’s. Also, like DarkSide, this is stored in the same folder on disk (C:\ProgramData), with an identical file size (2,818,366 bytes), image format (.BMP) and image size (1706 x 826 pixels, 16-bit color depth.)


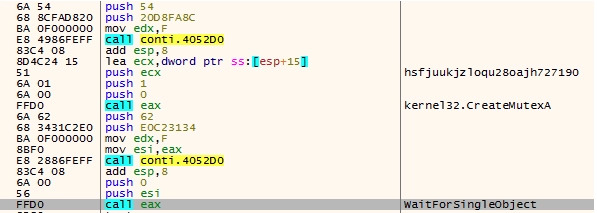
Like DarkSide (and REvil), BlackMatter uses a run-time API that can hinder static analysis of the malware. And like the other two ransomware groups, strings are also encrypted and revealed during runtime. While both of these techniques are common across many recent malware, the way in which the runtime API and string decryption function in BlackMatter is very similar to the functionality seen in DarkSide and REvil.

In another shared similarity with both REvil and Darkside, BlackMatter ransomware stores configuration information in the binary in an encoded format. SophosLabs decoded this and found that BlackMatter ransomware has a similar structure and information stored in the configuration blob, like lists of processes and services to kill, the ransom note, C2 details, directories to avoid etc.
The ransomware can encrypt open (locked) documents. BlackMatter terminates several productivity-related processes before encryption begins:
- ensvc
- thebat
- mydesktopqos
- xfssvccon
- firefox
- infopath
- winword
- steam
- synctime
- notepad
- ocomm
- onenote
- mspub
- thunderbird
- agensvc
- sql
- excel
- powerpnt
- outlook
- wordpad
- dbeng50
- isqlplussvc
- sqbcoreservice
- oracle
- ocautoupds
- dbsnmp
- msaccess
- tbirdconfig
- ocssd
- mydesktopservice
- visio
The BlackMatter ransomware collects information from victim machines, like hostname, logged in user, operating system, domain name, system type (architecture), language, as well as the size of the disk and available free space.

The analyzed sample sends these details to a remote server hosted on paymenthacks.com. It uses a specific header to post the information.
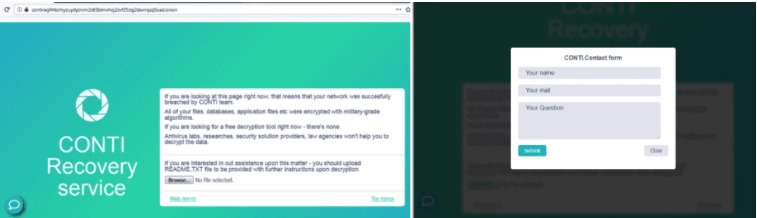
The BlackMatter ransomware drops a ransom note in user-accessible folders on the disk.

Protection
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.