JVCKenwood has been infected in a Conti Ransomware attack where the hackers have stolen 1.7TB of data and are demanding a ransom fee of $7 Million.
JVCKenwood is a multinational electronics company based out of Japan that employs 16,956 people and has a 2021 revenue of $2.45 billion. The company is known for its brands JVC, Kenwood, and Victor, which manufacture car and home audio equipment, healthcare and radio equipment, professional and in-vehicle cameras, and portable power stations.
This week, the company disclosed that servers belonging to its sales division in Europe were hacked on September 22nd, and the Conti Ransomware gang accessed and stole data during the incident.
“JVCKENWOOD detected unauthorized access on September 22, 2021 to the servers operated by some of the JVCKENWOOD Group’s sales companies in Europe. It was found that there was a possibility of information leak by the third party who made the unauthorized access,” JVCKENWOOD announced in a press statement.
“Currently, a detailed investigation is being conducted by the specialized agency outside the company in collaboration with the relevant authorities. No customer data leak has been confirmed at this time. The details will be announced on the company website as soon as they become available.”
The ransom note left by Conti Ransomware has been shared by several media sources since.
In the negotiation chat, the Conti Ransomware gang claims to have stolen 1.5 TB of files and is demanding $7 million not to publish the data and provide a file decryptor.
In an attempt to up the credibility of the attack, the gang shared a PDF file indicating it is a scanned passport for a JVCKenwood employee.
It is believed that there has been no further contact from the JVCKenwood representative, possibly indicating the company will not pay the ransomware.
Conti is a ransomware family believed to be operated by the TrickBot threat actor group and is commonly installed after networks are compromised by the TrickBot, BazarBackdoor, and Anchor trojans.
Conti Ransomware has been responsible for a range of attacks, especially in the last 12 months. These include high-profile attacks against the City of Tulsa, Ireland’s Health Service Executive (HSE), Advantech, and numerous health care organizations.
Last week, a joint report between the FBI, CISA, and NSA warned of escalating Conti ransomware attacks.
Conti Ransomware Analysis

Note: The Analysis of Conti Ransomware was carried out by researchers at Vipre Labs.
Conti ransomware encrypts the files of their victims and publishes the data on their website similar to what other strains do. This extortion behavior is visible on their ransom note saying “We’ve downloaded your data and are ready to publish it on our news website”.
When executed, it will start to encrypt files and change the file extension of the encrypted files to .ODMUA. Like other ransomware, it will leave a ransom note that has a filename “readme.txt”.
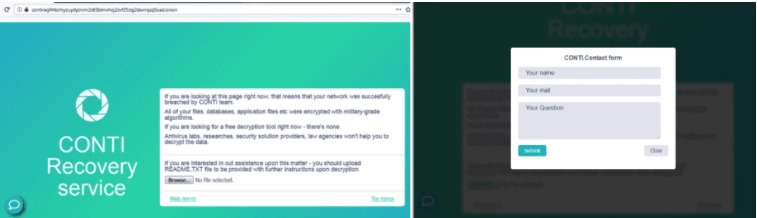
The Conti ransomware website has an instruction on how to upload the README.txt for the decryption and a contact button at the bottom left of the page. Once you click the contact button, a form will appear where you will provide your contact information and question as shown below.
Conti ransomware will perform a known malware technique called process hollowing. It is where the malware will create a process in a suspended state, unmaps or removes the PE image layout from a given process space using ZwUnmapViewofSection function, write it’s malicious code using WriteProcessMemory, set a new entry point using SetThreadContext, and resume the execution of the suspended process using the ResumeThread function.
Upon research, we found out that the use of -p argument is to encrypt a specific directory with a single thread and the -m argument is to encrypt the files with multiple threads. It means that Conti ransomware has a multi-threading capability. Multi-threading is where main ransomware creates child threads to speed up the encryption.
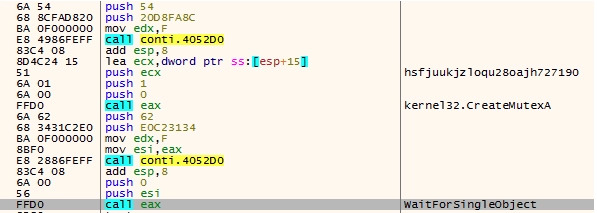
It will use a string “hsfjuukjzloqu28oajh727190” that was decrypted using the decryption of string routine mentioned above for creating a mutex using CreateMutexA function. Then check if there’s an already running mutex. This was commonly used by ransomware to avoid infecting the system more than once.
It will also delete all the shadow volume copies on the infected system to ensure that the victims won’t be able to recover their encrypted files.
After deleting the shadow copies, Conti ransomware will now start its file encryption by first creating the ransom note which will be first drop in C drive using “CreateFileW” and write the content of its ransom note using “WriteFile”.
As with other ransomware, it will utilize the functions “FindFirstFileW” and “FindNextFileW” to find the files they will encrypt. Conti ransomware has a list of files/file extension and directories which will be excluded for the infection.
When Conti finds the file to be encrypted, it will now generate keys that will be used to encrypt the files. It will used the handle returned by calling the function “CryptAcquireContext” that request a cryptographic context from the Microsoft Enhanced Cryptographic Provider, then the “CryptGenRandom” function to generate cryptographically random bytes, and “CryptEncrypt” function. It leverages AES 256 encryption for their infection.
Then it will open the target file using the “CreateFile” function and retrieve the size of the target file using “GetFileSize”. After this the malware will decrypt different file extensions and check if the file extension of the targeted file is in the list.
Conti ransomware will not just encrypt the files of the infected machine but also spreads and infects the other machine on the same network using SMB protocol.
Protection
Attacks like the Conti Ransomware campaign show that cyberattacks are increasing at an exponential rate, and both government and business leaders are underprepared to face the fallout of an attack. There are several tools internet users should use to increase their online protection. One of these tools is SaferNet.
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses face today. It not only connects every device using a secure, 24/7 always on, military grade VPN, but it also stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition to SaferNet’s VPN and cyber protection, it also offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling, and blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.