VPN Protection. VPNs, or virtual private networks, are one of the most heavily marketed tools advertised on the net today. VPN Protection is spoken about often, but rarely is this concept explained. What does a VPN protect against, and what doesn’t? Are all VPNs built the same? These are important questions, especially considering the vast differences between VPN providers.
But what is a VPN? A VPN, or virtual private network, is a digital tool with the core functionality of helping its users stay secure and private in the digital age. Though mostly privacy-focused, VPN Protection should be at the center of all conversations are VPNs.
Under the hood, extends a private network across a public network which allows users to send and receive data privately as if on a private network.
When a data packet is sent from the user, it sends it through the VPN. The VPN adds an Authentication Header (AH) for routing and authentication. This data is then encrypted, and enclosed with an Encapsulating Security Payload (ESP), which dictates how the data is handled.

The encryption process that occured here is the soul of a VPN. Encryption usually involves using a key to scramble and unscramble data being sent from your device. Only your device and the VPN provider have the decryption key – to everyone else, your data appears like a garbled mess.
There are different types of encryption that different VPN services use. But for the most part any major VPN service uses an acceptable level of encryption.
VPNs were considered a ‘nice to have, but not required’ tool for many years, but now in 2022, they truly a necessary tool.
VPNs were first conceived in 1996 by Gurdeep Singh-Pall. Singh-Pall was a Microsoft employee who invented PPTP (Point-to-Point Tunneling Protocol). PPTP was a critical element in implemented VPNs. The engineer did this to allow other Microsoft employees to have a secure Internet connection while working from home. Though starting as an in-house tool, this was the genesis of VPN technology as we know it today.
Since then, VPN technology has changed dramatically, though the core remained the same. There are different types of VPNs, and different protocols, such as L2TP/IPsec, OpenVPN, PPTP, SSTP. As mentioned earlier, there is also different types of encryption used, including hashing, symmetric, asymmetric.

Even today, encryption is changing and being improved upon constantly. The number of VPN users has increased too, with 1 in 4 internet users owning a VPN of some kind. However, this number is still not high enough in today’s world. VPN Protection truly is critical.
The basics of VPN Protection and the technology behind the tool has been laid out. Now, let’s take a look at some things VPNs can protect you against, and what they can’t.
5 Things VPNs Can Protect You Against
Download Monitoring

When you torrent or download files, your identity is not hidden from your internet service provider (ISP). This means that your ISP can see everything that you’re downloading. As well as ISPs, government and some advertisers can see what you’re downloading. If streaming or torrenting the likes of movies not available on your regular broadcasting servicers, this can lead to fines or harsher legal action. A VPN can prevent this. When connected to a VPN, the encryption applied to your connection will make your download activity seem garbled, and unreadable to anyone looking in.
Streaming/Gaming Monitoring
Both streaming and gaming can use a large amount of bandwidth, which is something ISPs want to avoid at all costs. If you game or stream a lot, your account may be flagged and your ISP may throttle your bandwidth during these sessions. This is also the case during peak 5pm-11pm hours, which is often when internet usage is high in many households.
Thankfully, a VPN can protect you here. Like with Downloading Monitoring, the VPN will scramble your activity, and you won’t be flagged by ISP automatic systems.
Search Engine / Activity Monitoring
Using a search engine, or visiting just about any website, will trigger several third parties to start monitoring your activity. Aside from governments and ISPs, a very command tracker here comes in the form of advertisers, who follow you around the web as best as they can.
To advertisers, the data metrics you supply are like gold, which can be sold on to other advertisers. While annoying, it is relatively harmless, but there are many more malicious advertisers out there trying to profile you based on your activity, and sell more aggresively and instruivly to you.
These are breaches of privacy and trust, and problems a VPN can solve.
A VPN will secure both your search history and general web activity. These include activity from your ISP, advertisers, government, and cybercriminals.
It is important to note that this activity is not hidden from your browser provider – Google, for example. It is advised to use a privacy-focused browser to remain as private as possible.

Packet Inspection Protection
Packet Inspection protection is an interesting topic and can easily be assumed to similar to activity monitoring, which it is.
Packets make up the blood of any internet interaction. Essentially they allow users to interact with websites, send emails, play video games – really any online activity. Packets are sent and received at an extremeley high rate per second.
Packet inspection then is a very real threat, and a common one too. Anyone inspecting the packets you send can figure out exactly what you’re doing.
When you have no encryption in place, all these packets can be inspected. A VPNs encryption protocols can act against this, and any onlookers will only see nonsensical code when trying to inspect the packets you send.
Man-in-the-Middle Attacks
A man-in-the-middle attack is similar to packet inspection, but goes a step further. While monitoring packets, a hacker can interject themselves into your activity – For example, accessing a online banking system.
In the classic case, these are performed over public wifi spaces such as airports and cafes. However given how accessible public wifi is around many of our cities, it has seen huge gains in popularity.
These attacks can be deadly, and when they happen when you use a banking service, they can cause lasting damage. A VPN encryption process will again prevent these attacks from taking place.

3 Things VPNs Don’t Protect You Against
Account Activity Monitoring
Despite an encrypted connection, account activity on certain platforms will still be monitored. These are most obvious in things like social media platforms – When using Facebook, Facebook will always see what you can do. As mentioned earlier, this goes for browser activity too depending on the browser provider. Try drift toward services that champion consumer privacy.
Online Identity Protection
100% online identity protection, that is to be 100% anonymous, is possible, but the steps to do so are so complex that they go beyond the scope of this article. For people using day-to-day internet, 100% anonymity isn’t possible.
However, much of this is on the users shoulders. If you reveal everything about yourself online, a VPN can do nothing for you. Practice good digital hyigene, and you can remain more anonymous online.
Malware – Hacking, Viruses, General Cybercrime
To preference this point – The overwhelming majority of VPNs, especially the popular ones, have zero malware protection. This is not always the case – But more on this later.
Cybercrime is a huge danger online, more than many internet users know.
There are a range of threats online facing users every second, including:
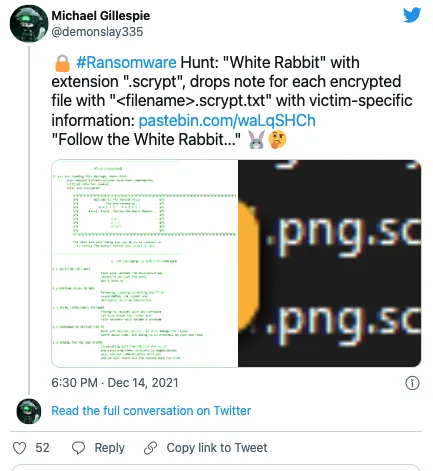
Ransomware – Ransomware is a type of malware that encrypts a victim’s device entirely. Ransomware then demands a monetary fee, or ransom, for the safe release of the data. During this time, the victim cannot access any of their files. Ransomware is a sophisticated type of virus, and will often laterally spread across a network. Ransomware can take down large scale organizations like hospitals in seconds. Though it only became more popular in the last decade, Ransomware has become the number one threat in the cybersecurity world. Ransomware operators can generate billions of dollars in a successful attack campaign.
Spyware – The primary goal of Spyware is to steal sensitive information and relay it back to some kind of server or service. This information could be anything – internet usage, what is typed on the device, camera or microphone activity – truly any activity that occurs on the device. This information can be relayed to a number of different entities. Very often, these are advertisers or big data companies. In more malicious cases, it could be sent to private servers belonging to a lone hacker, or hacking group.
Botnets – At its core, a Botnet is a network of hijacked host devices that are used in a number of illicit activities, chiefly cyberattacks. The word is a portmanteau of ‘robot’ and ‘network’. Botnets are primarily used to automate large scale attacks, or to distribute additional malware. Users are unaware if a device they own is infected. While infected, besides for carrying out attacks, the host device can also be used to infect nearby devices or devices in any part of the world.
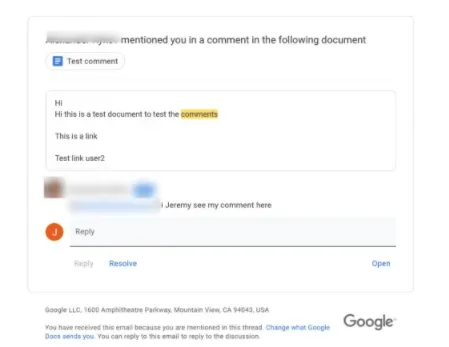
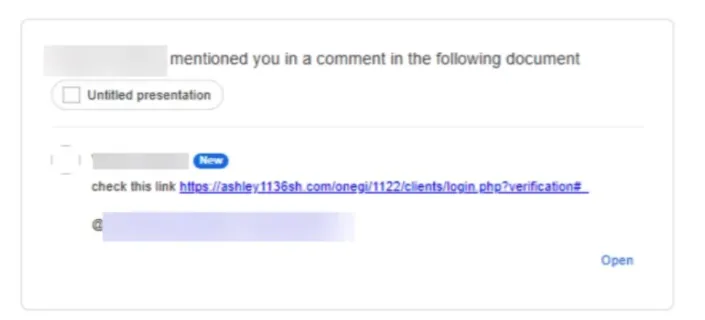
Phishing Attacks – Phishing is perhaps the most well-known attack vector a hacker can utilize. Nearly everyone has seen a phishing attempt at some point in their lives. To put it simply, Phishing is a cybercrime in which a target or targets are contacted by email, telephone or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking and credit card details, and passwords. Phishing is not necessarily all about grabbing credentials, though. Modern phishing methods often revolve around having the target download a file that is covertly malware or enabling macros on a Word document which in turn deploy a virus. Phishing and the act of social engineering come hand in hand.
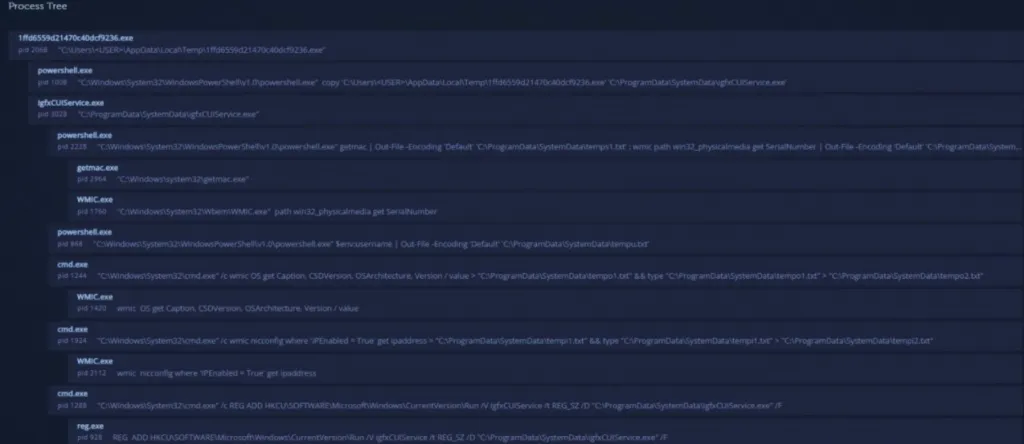
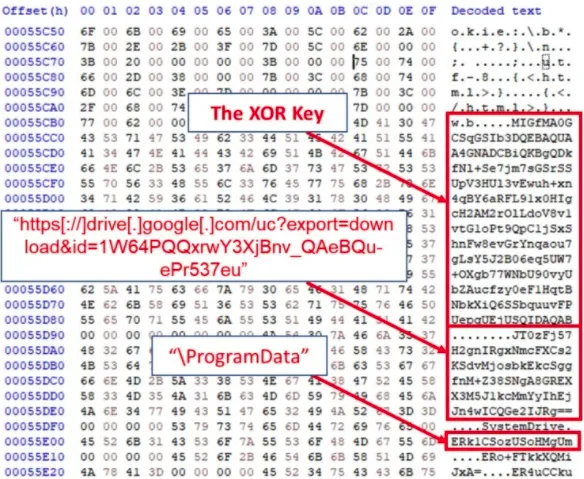
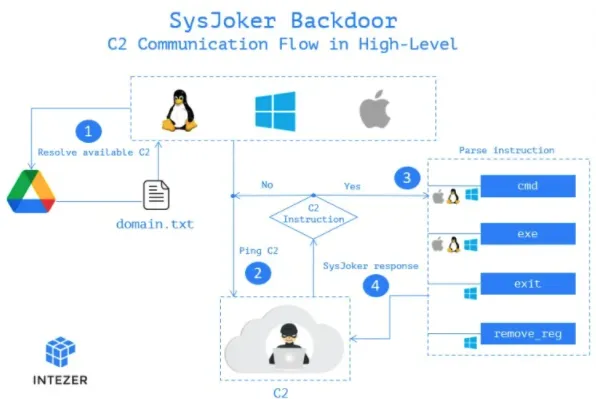
Remote Access Trojans – Remote Access Trojans, or RATs, are a type of malware capable of infecting just about any kind of device. These type of viruses allow hackers to remotely machine infected hosts, similar to products like Teamviewer. They are often spoken about in tandem with other malware strains such as Spyware, as the two share common traits. Different RATs have varying levels of complexity in their capabilities of monitoring and controlling infected devices. Usually, a remote access trojan will initialize the connection to a command and control center (C2). The C2 connects the machine to the hacker’s own. This will allow a hacker to send a number of commands back to the RAT, which will then execute on the host machine.
As stated, the majority of VPNs offer no anti-virus features. This is not the case for SaferNet’s always-on VPN, which was built with twin goals in mind – To offer both the privacy of a VPN and the antivirus capabilities of anti-malware software. While most services require a number of different software solutions to achieve both privacy and security, SaferNet gets it done all-in-one.
SaferNet: The First Name In VPN Protection
SaferNet is the perfect solution to the cybersecurity issues that individuals, families, and businesses. SaferNet connects every device using a secure, 24/7 always on, military grade VPN. SaferNet stops outside cyberthreats, malware and viruses as well. On SaferNet, all users are protected anywhere in the world, all the time, on any cellular or Wi-Fi network. In addition, SaferNet offers a range of employee or parental/family internet controls including internet filtering, monitoring, scheduling. Also, SaferNet offers blocking access to websites or even entire website categories
Typically, a business or family would need 3 separate services for a VPN, Malware Protection, and Internet Controls; SaferNet offers all 3 features in one service. SaferNet truly is an endpoint security presence that can be implemented in minutes around the world, on phones, laptops, tablets, and computers at an economical price point that caters to all sizes of businesses and families. SaferNet guarantees a smooth setup and installation process that takes only minutes, and an easily accessible control hub for you to monitor all your employee’s or family members devices; including activity, time spent online, and threats blocked.